- Engineering Mathematics
- Discrete Mathematics
- Operating System
- Computer Networks
- Digital Logic and Design
- C Programming
- Data Structures
- Theory of Computation
- Compiler Design
- Computer Org and Architecture
- Computer Network Tutorial

Basics of Computer Network
- Basics of Computer Networking
- Introduction to basic Networking Terminology
- Goals of Networks
- Basic characteristics of Computer Networks
- Challenges of Computer Network
- Physical Components of Computer Network
Network Hardware and Software
- Types of Computer Networks
- LAN Full Form
- How to Set Up a LAN Network?
- MAN Full Form in Computer Networking
- MAN Full Form
- WAN Full Form
- Introduction of Internetworking
- Difference between Internet, Intranet and Extranet
- Protocol Hierarchies in Computer Network
- Network Devices (Hub, Repeater, Bridge, Switch, Router, Gateways and Brouter)
- Introduction of a Router
- Introduction of Gateways
- What is a network switch, and how does it work?
Network Topology
- Types of Network Topology
- Difference between Physical and Logical Topology
- What is OSI Model? - Layers of OSI Model
- Physical Layer in OSI Model
- Data Link Layer
- Session Layer in OSI model
Presentation Layer in OSI model
- Application Layer in OSI Model
- Protocol and Standard in Computer Networks
- Examples of Data Link Layer Protocols
- TCP/IP Model
- TCP/IP Ports and Its Applications
- What is Transmission Control Protocol (TCP)?
- TCP 3-Way Handshake Process
- Services and Segment structure in TCP
- TCP Connection Establishment
- TCP Connection Termination
- Fast Recovery Technique For Loss Recovery in TCP
- Difference Between OSI Model and TCP/IP Model
Medium Access Control
- MAC Full Form
- Channel Allocation Problem in Computer Network
- Multiple Access Protocols in Computer Network
- Carrier Sense Multiple Access (CSMA)
- Collision Detection in CSMA/CD
- Controlled Access Protocols in Computer Network
SLIDING WINDOW PROTOCOLS
- Stop and Wait ARQ
- Sliding Window Protocol | Set 3 (Selective Repeat)
- Piggybacking in Computer Networks
IP Addressing
- What is IPv4?
- What is IPv6?
- Introduction of Classful IP Addressing
- Classless Addressing in IP Addressing
- Classful Vs Classless Addressing
- Classless Inter Domain Routing (CIDR)
- Supernetting in Network Layer
- Introduction To Subnetting
- Difference between Subnetting and Supernetting
- Types of Routing
- Difference between Static and Dynamic Routing
- Unicast Routing - Link State Routing
- Distance Vector Routing (DVR) Protocol
- Fixed and Flooding Routing algorithms
- Introduction of Firewall in Computer Network
Congestion Control Algorithms
- Congestion Control in Computer Networks
- Congestion Control techniques in Computer Networks
- Computer Network | Leaky bucket algorithm
- TCP Congestion Control
Network Switching
- Circuit Switching in Computer Network
- Message switching techniques
- Packet Switching and Delays in Computer Network
- Differences Between Virtual Circuits and Datagram Networks
Application Layer:DNS
- Domain Name System (DNS) in Application Layer
- Details on DNS
- Introduction to Electronic Mail
- E-Mail Format
- World Wide Web (WWW)
- HTTP Full Form
- Streaming Stored Video
- What is a Content Distribution Network and how does it work?
CN Interview Quetions
- Top 50 Networking Interview Questions (2024)
- Top 50 TCP/IP interview questions and answers
- Top 50 IP addressing interview questions and answers
- Last Minute Notes - Computer Networks
- Computer Network - Cheat Sheet
- Network Layer
- Transport Layer
- Application Layer
Prerequisite : OSI Model
Introduction : Presentation Layer is the 6th layer in the Open System Interconnection (OSI) model. This layer is also known as Translation layer, as this layer serves as a data translator for the network. The data which this layer receives from the Application Layer is extracted and manipulated here as per the required format to transmit over the network. The main responsibility of this layer is to provide or define the data format and encryption. The presentation layer is also called as Syntax layer since it is responsible for maintaining the proper syntax of the data which it either receives or transmits to other layer(s).
Functions of Presentation Layer :
The presentation layer, being the 6th layer in the OSI model, performs several types of functions, which are described below-
- Presentation layer format and encrypts data to be sent across the network.
- This layer takes care that the data is sent in such a way that the receiver will understand the information (data) and will be able to use the data efficiently and effectively.
- This layer manages the abstract data structures and allows high-level data structures (example- banking records), which are to be defined or exchanged.
- This layer carries out the encryption at the transmitter and decryption at the receiver.
- This layer carries out data compression to reduce the bandwidth of the data to be transmitted (the primary goal of data compression is to reduce the number of bits which is to be transmitted).
- This layer is responsible for interoperability (ability of computers to exchange and make use of information) between encoding methods as different computers use different encoding methods.
- This layer basically deals with the presentation part of the data.
- Presentation layer, carries out the data compression (number of bits reduction while transmission), which in return improves the data throughput.
- This layer also deals with the issues of string representation.
- The presentation layer is also responsible for integrating all the formats into a standardized format for efficient and effective communication.
- This layer encodes the message from the user-dependent format to the common format and vice-versa for communication between dissimilar systems.
- This layer deals with the syntax and semantics of the messages.
- This layer also ensures that the messages which are to be presented to the upper as well as the lower layer should be standardized as well as in an accurate format too.
- Presentation layer is also responsible for translation, formatting, and delivery of information for processing or display.
- This layer also performs serialization (process of translating a data structure or an object into a format that can be stored or transmitted easily).
Features of Presentation Layer in the OSI model: Presentation layer, being the 6th layer in the OSI model, plays a vital role while communication is taking place between two devices in a network.
List of features which are provided by the presentation layer are:
- Presentation layer could apply certain sophisticated compression techniques, so fewer bytes of data are required to represent the information when it is sent over the network.
- If two or more devices are communicating over an encrypted connection, then this presentation layer is responsible for adding encryption on the sender’s end as well as the decoding the encryption on the receiver’s end so that it can represent the application layer with unencrypted, readable data.
- This layer formats and encrypts data to be sent over a network, providing freedom from compatibility problems.
- This presentation layer also negotiates the Transfer Syntax.
- This presentation layer is also responsible for compressing data it receives from the application layer before delivering it to the session layer (which is the 5th layer in the OSI model) and thus improves the speed as well as the efficiency of communication by minimizing the amount of the data to be transferred.
Working of Presentation Layer in the OSI model : Presentation layer in the OSI model, as a translator, converts the data sent by the application layer of the transmitting node into an acceptable and compatible data format based on the applicable network protocol and architecture. Upon arrival at the receiving computer, the presentation layer translates data into an acceptable format usable by the application layer. Basically, in other words, this layer takes care of any issues occurring when transmitted data must be viewed in a format different from the original format. Being the functional part of the OSI mode, the presentation layer performs a multitude (large number of) data conversion algorithms and character translation functions. Mainly, this layer is responsible for managing two network characteristics: protocol (set of rules) and architecture.
Presentation Layer Protocols : Presentation layer being the 6th layer, but the most important layer in the OSI model performs several types of functionalities, which makes sure that data which is being transferred or received should be accurate or clear to all the devices which are there in a closed network. Presentation Layer, for performing translations or other specified functions, needs to use certain protocols which are defined below –
- Apple Filing Protocol (AFP): Apple Filing Protocol is the proprietary network protocol (communications protocol) that offers services to macOS or the classic macOS. This is basically the network file control protocol specifically designed for Mac-based platforms.
- Lightweight Presentation Protocol (LPP): Lightweight Presentation Protocol is that protocol which is used to provide ISO presentation services on the top of TCP/IP based protocol stacks.
- NetWare Core Protocol (NCP): NetWare Core Protocol is the network protocol which is used to access file, print, directory, clock synchronization, messaging, remote command execution and other network service functions.
- Network Data Representation (NDR): Network Data Representation is basically the implementation of the presentation layer in the OSI model, which provides or defines various primitive data types, constructed data types and also several types of data representations.
- External Data Representation (XDR): External Data Representation (XDR) is the standard for the description and encoding of data. It is useful for transferring data between computer architectures and has been used to communicate data between very diverse machines. Converting from local representation to XDR is called encoding, whereas converting XDR into local representation is called decoding.
- Secure Socket Layer (SSL): The Secure Socket Layer protocol provides security to the data that is being transferred between the web browser and the server. SSL encrypts the link between a web server and a browser, which ensures that all data passed between them remains private and free from attacks.
Please Login to comment...
Similar reads.

Improve your Coding Skills with Practice
What kind of Experience do you want to share?
Layer 6 Presentation Layer
De/Encryption, Encoding, String representation
The presentation layer (data presentation layer, data provision level) sets the system-dependent representation of the data (for example, ASCII, EBCDIC) into an independent form, enabling the syntactically correct data exchange between different systems. Also, functions such as data compression and encryption are guaranteed that data to be sent by the application layer of a system that can be read by the application layer of another system to the layer 6. The presentation layer. If necessary, the presentation layer acts as a translator between different data formats, by making an understandable for both systems data format, the ASN.1 (Abstract Syntax Notation One) used.
OSI Layer 6 - Presentation Layer
The presentation layer is responsible for the delivery and formatting of information to the application layer for further processing or display. It relieves the application layer of concern regarding syntactical differences in data representation within the end-user systems. An example of a presentation service would be the conversion of an EBCDIC-coded text computer file to an ASCII-coded file. The presentation layer is the lowest layer at which application programmers consider data structure and presentation, instead of simply sending data in the form of datagrams or packets between hosts. This layer deals with issues of string representation - whether they use the Pascal method (an integer length field followed by the specified amount of bytes) or the C/C++ method (null-terminated strings, e.g. "thisisastring\0"). The idea is that the application layer should be able to point at the data to be moved, and the presentation layer will deal with the rest. Serialization of complex data structures into flat byte-strings (using mechanisms such as TLV or XML) can be thought of as the key functionality of the presentation layer. Encryption is typically done at this level too, although it can be done on the application, session, transport, or network layers, each having its own advantages and disadvantages. Decryption is also handled at the presentation layer. For example, when logging on to bank account sites the presentation layer will decrypt the data as it is received.[1] Another example is representing structure, which is normally standardized at this level, often by using XML. As well as simple pieces of data, like strings, more complicated things are standardized in this layer. Two common examples are 'objects' in object-oriented programming, and the exact way that streaming video is transmitted. In many widely used applications and protocols, no distinction is made between the presentation and application layers. For example, HyperText Transfer Protocol (HTTP), generally regarded as an application-layer protocol, has presentation-layer aspects such as the ability to identify character encoding for proper conversion, which is then done in the application layer. Within the service layering semantics of the OSI network architecture, the presentation layer responds to service requests from the application layer and issues service requests to the session layer. In the OSI model: the presentation layer ensures the information that the application layer of one system sends out is readable by the application layer of another system. For example, a PC program communicates with another computer, one using extended binary coded decimal interchange code (EBCDIC) and the other using ASCII to represent the same characters. If necessary, the presentation layer might be able to translate between multiple data formats by using a common format. Wikipedia
- Data conversion
- Character code translation
- Compression
- Encryption and Decryption
The Presentation OSI Layer is usually composed of 2 sublayers that are:
CASE common application service element
Sase specific application service element, layer 7 application layer, layer 6 presentation layer, layer 5 session layer, layer 4 transport layer, layer 3 network layer, layer 2 data link layer, layer 1 physical layer.
The OSI Model – The 7 Layers of Networking Explained in Plain English

This article explains the Open Systems Interconnection (OSI) model and the 7 layers of networking, in plain English.
The OSI model is a conceptual framework that is used to describe how a network functions. In plain English, the OSI model helped standardize the way computer systems send information to each other.
Learning networking is a bit like learning a language - there are lots of standards and then some exceptions. Therefore, it’s important to really understand that the OSI model is not a set of rules. It is a tool for understanding how networks function.
Once you learn the OSI model, you will be able to further understand and appreciate this glorious entity we call the Internet, as well as be able to troubleshoot networking issues with greater fluency and ease.
All hail the Internet!
Prerequisites
You don’t need any prior programming or networking experience to understand this article. However, you will need:
- Basic familiarity with common networking terms (explained below)
- A curiosity about how things work :)
Learning Objectives
Over the course of this article, you will learn:
- What the OSI model is
- The purpose of each of the 7 layers
- The problems that can happen at each of the 7 layers
- The difference between TCP/IP model and the OSI model
Common Networking Terms
Here are some common networking terms that you should be familiar with to get the most out of this article. I’ll use these terms when I talk about OSI layers next.
A node is a physical electronic device hooked up to a network, for example a computer, printer, router, and so on. If set up properly, a node is capable of sending and/or receiving information over a network.
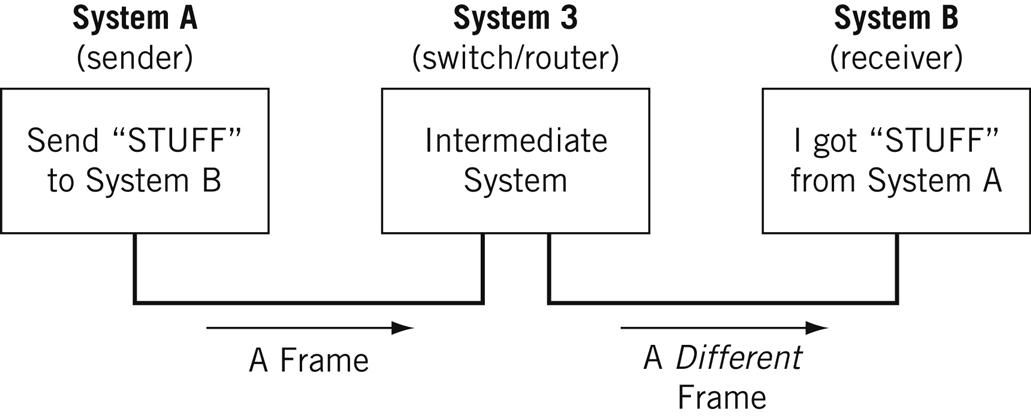
Nodes may be set up adjacent to one other, wherein Node A can connect directly to Node B, or there may be an intermediate node, like a switch or a router, set up between Node A and Node B.
Typically, routers connect networks to the Internet and switches operate within a network to facilitate intra-network communication. Learn more about hub vs. switch vs. router.
Here's an example:
For the nitpicky among us (yep, I see you), host is another term that you will encounter in networking. I will define a host as a type of node that requires an IP address. All hosts are nodes, but not all nodes are hosts. Please Tweet angrily at me if you disagree.
Links connect nodes on a network. Links can be wired, like Ethernet, or cable-free, like WiFi.
Links to can either be point-to-point, where Node A is connected to Node B, or multipoint, where Node A is connected to Node B and Node C.
When we’re talking about information being transmitted, this may also be described as a one-to-one vs. a one-to-many relationship.
A protocol is a mutually agreed upon set of rules that allows two nodes on a network to exchange data.
“A protocol defines the rules governing the syntax (what can be communicated), semantics (how it can be communicated), and synchronization (when and at what speed it can be communicated) of the communications procedure. Protocols can be implemented on hardware, software, or a combination of both. Protocols can be created by anyone, but the most widely adopted protocols are based on standards.” - The Illustrated Network.
Both wired and cable-free links can have protocols.
While anyone can create a protocol, the most widely adopted protocols are often based on standards published by Internet organizations such as the Internet Engineering Task Force (IETF).
A network is a general term for a group of computers, printers, or any other device that wants to share data.
Network types include LAN, HAN, CAN, MAN, WAN, BAN, or VPN. Think I’m just randomly rhyming things with the word can ? I can ’t say I am - these are all real network types. Learn more here .
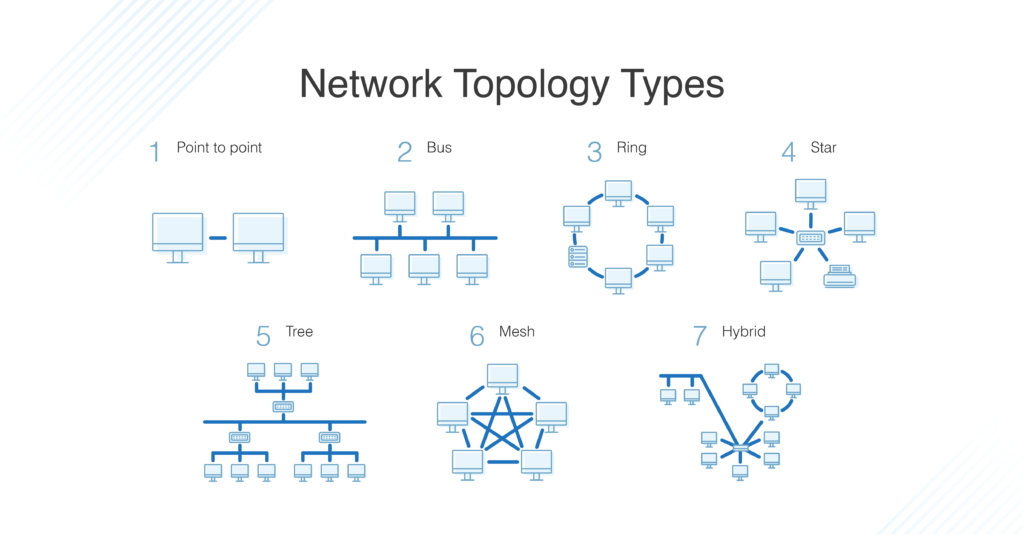
Topology describes how nodes and links fit together in a network configuration, often depicted in a diagram. Here are some common network topology types:
A network consists of nodes, links between nodes, and protocols that govern data transmission between nodes.
At whatever scale and complexity networks get to, you will understand what’s happening in all computer networks by learning the OSI model and 7 layers of networking.
What is the OSI Model?
The OSI model consists of 7 layers of networking.
First, what’s a layer?

No, a layer - not a lair . Here there are no dragons.
A layer is a way of categorizing and grouping functionality and behavior on and of a network.
In the OSI model, layers are organized from the most tangible and most physical, to less tangible and less physical but closer to the end user.
Each layer abstracts lower level functionality away until by the time you get to the highest layer. All the details and inner workings of all the other layers are hidden from the end user.
How to remember all the names of the layers? Easy.
- Please | Physical Layer
- Do | Data Link Layer
- Not | Network Layer
- Tell (the) | Transport Layer
- Secret | Session Layer
- Password (to) | Presentation Layer
- Anyone | Application Layer
Keep in mind that while certain technologies, like protocols, may logically “belong to” one layer more than another, not all technologies fit neatly into a single layer in the OSI model. For example, Ethernet, 802.11 (Wifi) and the Address Resolution Protocol (ARP) procedure operate on >1 layer.
The OSI is a model and a tool, not a set of rules.
OSI Layer 1
Layer 1 is the physical layer . There’s a lot of technology in Layer 1 - everything from physical network devices, cabling, to how the cables hook up to the devices. Plus if we don’t need cables, what the signal type and transmission methods are (for example, wireless broadband).
Instead of listing every type of technology in Layer 1, I’ve created broader categories for these technologies. I encourage readers to learn more about each of these categories:
- Nodes (devices) and networking hardware components. Devices include hubs, repeaters, routers, computers, printers, and so on. Hardware components that live inside of these devices include antennas, amplifiers, Network Interface Cards (NICs), and more.
- Device interface mechanics. How and where does a cable connect to a device (cable connector and device socket)? What is the size and shape of the connector, and how many pins does it have? What dictates when a pin is active or inactive?
- Functional and procedural logic. What is the function of each pin in the connector - send or receive? What procedural logic dictates the sequence of events so a node can start to communicate with another node on Layer 2?
- Cabling protocols and specifications. Ethernet (CAT), USB, Digital Subscriber Line (DSL) , and more. Specifications include maximum cable length, modulation techniques, radio specifications, line coding, and bits synchronization (more on that below).
- Cable types. Options include shielded or unshielded twisted pair, untwisted pair, coaxial and so on. Learn more about cable types here .
- Signal type. Baseband is a single bit stream at a time, like a railway track - one-way only. Broadband consists of multiple bit streams at the same time, like a bi-directional highway.
- Signal transmission method (may be wired or cable-free). Options include electrical (Ethernet), light (optical networks, fiber optics), radio waves (802.11 WiFi, a/b/g/n/ac/ax variants or Bluetooth). If cable-free, then also consider frequency: 2.5 GHz vs. 5 GHz. If it’s cabled, consider voltage. If cabled and Ethernet, also consider networking standards like 100BASE-T and related standards.
The data unit on Layer 1 is the bit.
A bit the smallest unit of transmittable digital information. Bits are binary, so either a 0 or a 1. Bytes, consisting of 8 bits, are used to represent single characters, like a letter, numeral, or symbol.
Bits are sent to and from hardware devices in accordance with the supported data rate (transmission rate, in number of bits per second or millisecond) and are synchronized so the number of bits sent and received per unit of time remains consistent (this is called bit synchronization). The way bits are transmitted depends on the signal transmission method.
Nodes can send, receive, or send and receive bits. If they can only do one, then the node uses a simplex mode. If they can do both, then the node uses a duplex mode. If a node can send and receive at the same time, it’s full-duplex – if not, it’s just half-duplex.
The original Ethernet was half-duplex. Full-duplex Ethernet is an option now, given the right equipment.
How to Troubleshoot OSI Layer 1 Problems
Here are some Layer 1 problems to watch out for:
- Defunct cables, for example damaged wires or broken connectors
- Broken hardware network devices, for example damaged circuits
- Stuff being unplugged (...we’ve all been there)
If there are issues in Layer 1, anything beyond Layer 1 will not function properly.
Layer 1 contains the infrastructure that makes communication on networks possible.
It defines the electrical, mechanical, procedural, and functional specifications for activating, maintaining, and deactivating physical links between network devices. - Source
Fun fact: deep-sea communications cables transmit data around the world. This map will blow your mind: https://www.submarinecablemap.com/
And because you made it this far, here’s a koala:

OSI Layer 2
Layer 2 is the data link layer . Layer 2 defines how data is formatted for transmission, how much data can flow between nodes, for how long, and what to do when errors are detected in this flow.
In more official tech terms:
- Line discipline. Who should talk for how long? How long should nodes be able to transit information for?
- Flow control. How much data should be transmitted?
- Error control - detection and correction . All data transmission methods have potential for errors, from electrical spikes to dirty connectors. Once Layer 2 technologies tell network administrators about an issue on Layer 2 or Layer 1, the system administrator can correct for those errors on subsequent layers. Layer 2 is mostly concerned with error detection, not error correction. ( Source )
There are two distinct sublayers within Layer 2:
- Media Access Control (MAC): the MAC sublayer handles the assignment of a hardware identification number, called a MAC address, that uniquely identifies each device on a network. No two devices should have the same MAC address. The MAC address is assigned at the point of manufacturing. It is automatically recognized by most networks. MAC addresses live on Network Interface Cards (NICs). Switches keep track of all MAC addresses on a network. Learn more about MAC addresses on PC Mag and in this article . Learn more about network switches here .
- Logical Link Control (LLC): the LLC sublayer handles framing addressing and flow control. The speed depends on the link between nodes, for example Ethernet or Wifi.
The data unit on Layer 2 is a frame .
Each frame contains a frame header, body, and a frame trailer:
- Header: typically includes MAC addresses for the source and destination nodes.
- Body: consists of the bits being transmitted.
- Trailer: includes error detection information. When errors are detected, and depending on the implementation or configuration of a network or protocol, frames may be discarded or the error may be reported up to higher layers for further error correction. Examples of error detection mechanisms: Cyclic Redundancy Check (CRC) and Frame Check Sequence (FCS). Learn more about error detection techniques here .
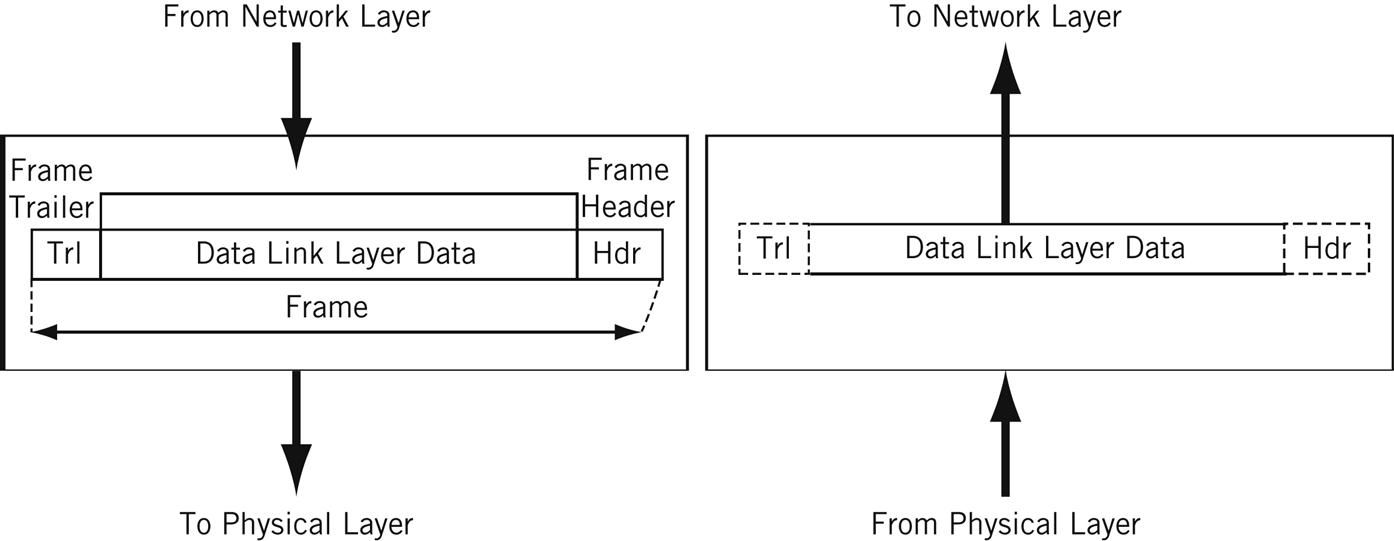
Typically there is a maximum frame size limit, called an Maximum Transmission Unit, MTU. Jumbo frames exceed the standard MTU, learn more about jumbo frames here .
How to Troubleshoot OSI Layer 2 Problems
Here are some Layer 2 problems to watch out for:
- All the problems that can occur on Layer 1
- Unsuccessful connections (sessions) between two nodes
- Sessions that are successfully established but intermittently fail
- Frame collisions
The Data Link Layer allows nodes to communicate with each other within a local area network. The foundations of line discipline, flow control, and error control are established in this layer.
OSI Layer 3
Layer 3 is the network layer . This is where we send information between and across networks through the use of routers. Instead of just node-to-node communication, we can now do network-to-network communication.
Routers are the workhorse of Layer 3 - we couldn’t have Layer 3 without them. They move data packets across multiple networks.
Not only do they connect to Internet Service Providers (ISPs) to provide access to the Internet, they also keep track of what’s on its network (remember that switches keep track of all MAC addresses on a network), what other networks it’s connected to, and the different paths for routing data packets across these networks.
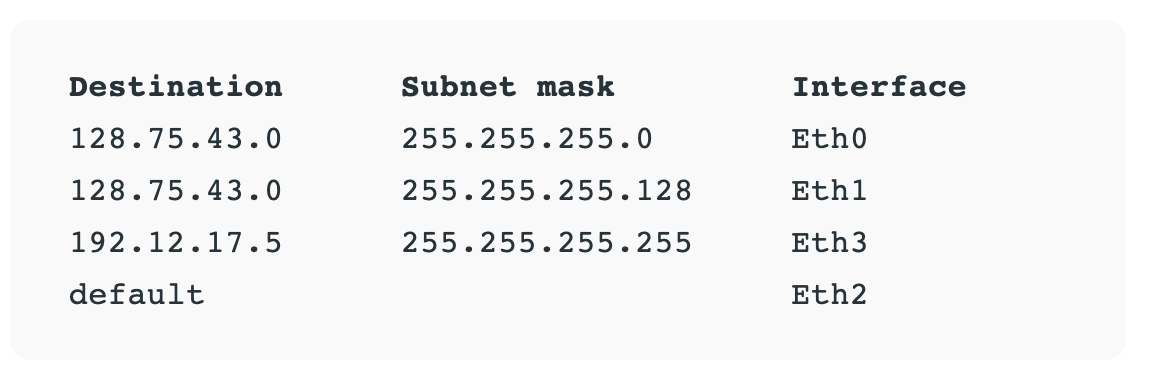
Routers store all of this addressing and routing information in routing tables.
Here’s a simple example of a routing table:
The data unit on Layer 3 is the data packet . Typically, each data packet contains a frame plus an IP address information wrapper. In other words, frames are encapsulated by Layer 3 addressing information.
The data being transmitted in a packet is also sometimes called the payload . While each packet has everything it needs to get to its destination, whether or not it makes it there is another story.
Layer 3 transmissions are connectionless, or best effort - they don't do anything but send the traffic where it’s supposed to go. More on data transport protocols on Layer 4.
Once a node is connected to the Internet, it is assigned an Internet Protocol (IP) address, which looks either like 172.16. 254.1 (IPv4 address convention) or like 2001:0db8:85a3:0000:0000:8a2e:0370:7334 (IPv6 address convention). Routers use IP addresses in their routing tables.
IP addresses are associated with the physical node’s MAC address via the Address Resolution Protocol (ARP), which resolves MAC addresses with the node’s corresponding IP address.
ARP is conventionally considered part of Layer 2, but since IP addresses don’t exist until Layer 3, it’s also part of Layer 3.
How to Troubleshoot OSI Layer 3 Problems
Here are some Layer 3 problems to watch out for:
- All the problems that can crop up on previous layers :)
- Faulty or non-functional router or other node
- IP address is incorrectly configured
Many answers to Layer 3 questions will require the use of command-line tools like ping , trace , show ip route , or show ip protocols . Learn more about troubleshooting on layer 1-3 here .
The Network Layer allows nodes to connect to the Internet and send information across different networks.
OSI Layer 4
Layer 4 is the transport layer . This where we dive into the nitty gritty specifics of the connection between two nodes and how information is transmitted between them. It builds on the functions of Layer 2 - line discipline, flow control, and error control.
This layer is also responsible for data packet segmentation, or how data packets are broken up and sent over the network.
Unlike the previous layer, Layer 4 also has an understanding of the whole message, not just the contents of each individual data packet. With this understanding, Layer 4 is able to manage network congestion by not sending all the packets at once.
The data units of Layer 4 go by a few names. For TCP, the data unit is a packet. For UDP, a packet is referred to as a datagram. I’ll just use the term data packet here for the sake of simplicity.
Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) are two of the most well-known protocols in Layer 4.
TCP, a connection-oriented protocol, prioritizes data quality over speed.
TCP explicitly establishes a connection with the destination node and requires a handshake between the source and destination nodes when data is transmitted. The handshake confirms that data was received. If the destination node does not receive all of the data, TCP will ask for a retry.
TCP also ensures that packets are delivered or reassembled in the correct order. Learn more about TCP here .
UDP, a connectionless protocol, prioritizes speed over data quality. UDP does not require a handshake, which is why it’s called connectionless.
Because UDP doesn’t have to wait for this acknowledgement, it can send data at a faster rate, but not all of the data may be successfully transmitted and we’d never know.
If information is split up into multiple datagrams, unless those datagrams contain a sequence number, UDP does not ensure that packets are reassembled in the correct order. Learn more about UDP here .
TCP and UDP both send data to specific ports on a network device, which has an IP address. The combination of the IP address and the port number is called a socket.
Learn more about sockets here .
Learn more about the differences and similarities between these two protocols here .
How to Troubleshoot OSI Layer 4 Problems
Here are some Layer 4 problems to watch out for:
- Blocked ports - check your Access Control Lists (ACL) & firewalls
- Quality of Service (QoS) settings. QoS is a feature of routers/switches that can prioritize traffic, and they can really muck things up. Learn more about QoS here .
The Transport Layer provides end-to-end transmission of a message by segmenting a message into multiple data packets; the layer supports connection-oriented and connectionless communication.
OSI Layer 5
Layer 5 is the session layer . This layer establishes, maintains, and terminates sessions.
A session is a mutually agreed upon connection that is established between two network applications. Not two nodes! Nope, we’ve moved on from nodes. They were so Layer 4.
Just kidding, we still have nodes, but Layer 5 doesn’t need to retain the concept of a node because that’s been abstracted out (taken care of) by previous layers.
So a session is a connection that is established between two specific end-user applications. There are two important concepts to consider here:
- Client and server model: the application requesting the information is called the client, and the application that has the requested information is called the server.
- Request and response model: while a session is being established and during a session, there is a constant back-and-forth of requests for information and responses containing that information or “hey, I don’t have what you’re requesting.”
Sessions may be open for a very short amount of time or a long amount of time. They may fail sometimes, too.
Depending on the protocol in question, various failure resolution processes may kick in. Depending on the applications/protocols/hardware in use, sessions may support simplex, half-duplex, or full-duplex modes.
Examples of protocols on Layer 5 include Network Basic Input Output System (NetBIOS) and Remote Procedure Call Protocol (RPC), and many others.
From here on out (layer 5 and up), networks are focused on ways of making connections to end-user applications and displaying data to the user.
How to Troubleshoot OSI Layer 5 Problems
Here are some Layer 5 problems to watch out for:
- Servers are unavailable
- Servers are incorrectly configured, for example Apache or PHP configs
- Session failure - disconnect, timeout, and so on.
The Session Layer initiates, maintains, and terminates connections between two end-user applications. It responds to requests from the presentation layer and issues requests to the transport layer.
OSI Layer 6
Layer 6 is the presentation layer . This layer is responsible for data formatting, such as character encoding and conversions, and data encryption.
The operating system that hosts the end-user application is typically involved in Layer 6 processes. This functionality is not always implemented in a network protocol.
Layer 6 makes sure that end-user applications operating on Layer 7 can successfully consume data and, of course, eventually display it.
There are three data formatting methods to be aware of:
- American Standard Code for Information Interchange (ASCII): this 7-bit encoding technique is the most widely used standard for character encoding. One superset is ISO-8859-1, which provides most of the characters necessary for languages spoken in Western Europe.
- Extended Binary-Coded Decimal Interchange Code (EBDCIC): designed by IBM for mainframe usage. This encoding is incompatible with other character encoding methods.
- Unicode: character encodings can be done with 32-, 16-, or 8-bit characters and attempts to accommodate every known, written alphabet.
Learn more about character encoding methods in this article , and also here .
Encryption: SSL or TLS encryption protocols live on Layer 6. These encryption protocols help ensure that transmitted data is less vulnerable to malicious actors by providing authentication and data encryption for nodes operating on a network. TLS is the successor to SSL.
How to Troubleshoot OSI Layer 6 Problems
Here are some Layer 6 problems to watch out for:
- Non-existent or corrupted drivers
- Incorrect OS user access level
The Presentation Layer formats and encrypts data.
OSI Layer 7
Layer 7 is the application layer .
True to its name, this is the layer that is ultimately responsible for supporting services used by end-user applications. Applications include software programs that are installed on the operating system, like Internet browsers (for example, Firefox) or word processing programs (for example, Microsoft Word).
Applications can perform specialized network functions under the hood and require specialized services that fall under the umbrella of Layer 7.
Electronic mail programs, for example, are specifically created to run over a network and utilize networking functionality, such as email protocols, which fall under Layer 7.
Applications will also control end-user interaction, such as security checks (for example, MFA), identification of two participants, initiation of an exchange of information, and so on.
Protocols that operate on this level include File Transfer Protocol (FTP), Secure Shell (SSH), Simple Mail Transfer Protocol (SMTP), Internet Message Access Protocol (IMAP), Domain Name Service (DNS), and Hypertext Transfer Protocol (HTTP).
While each of these protocols serve different functions and operate differently, on a high level they all facilitate the communication of information. ( Source )
How to Troubleshoot OSI Layer 7 Problems
Here are some Layer 7 problems to watch out for:
- All issues on previous layers
- Incorrectly configured software applications
- User error (... we’ve all been there)
The Application Layer owns the services and functions that end-user applications need to work. It does not include the applications themselves.
Our Layer 1 koala is all grown up.

Learning check - can you apply makeup to a koala?
Don’t have a koala?
Well - answer these questions instead. It’s the next best thing, I promise.
- What is the OSI model?
- What are each of the layers?
- How could I use this information to troubleshoot networking issues?
Congratulations - you’ve taken one step farther to understanding the glorious entity we call the Internet.
Learning Resources
Many, very smart people have written entire books about the OSI model or entire books about specific layers. I encourage readers to check out any O’Reilly-published books about the subject or about network engineering in general.
Here are some resources I used when writing this article:
- The Illustrated Network, 2nd Edition
- Protocol Data Unit (PDU): https://www.geeksforgeeks.org/difference-between-segments-packets-and-frames/
- Troubleshooting Along the OSI Model: https://www.pearsonitcertification.com/articles/article.aspx?p=1730891
- The OSI Model Demystified: https://www.youtube.com/watch?v=HEEnLZV2wGI
- OSI Model for Dummies: https://www.dummies.com/programming/networking/layers-in-the-osi-model-of-a-computer-network/
Chloe Tucker is an artist and computer science enthusiast based in Portland, Oregon. As a former educator, she's continuously searching for the intersection of learning and teaching, or technology and art. Reach out to her on Twitter @_chloetucker and check out her website at chloe.dev .
Read more posts .
If you read this far, thank the author to show them you care. Say Thanks
Learn to code for free. freeCodeCamp's open source curriculum has helped more than 40,000 people get jobs as developers. Get started
OSI Seven Layers Model Explained with Examples
This tutorial explains the OSI reference model. Learn the seven layers of the OSI model and the functions of each layer in detail through examples.
The OSI (Open System Interconnection) reference model is a comprehensive set of standards and rules for hardware manufacturers and software developers. By following these standards, they can build networking components and software applications that work in any environment. It was published in 1984 by ISO (International Organization for Standardization).
It provides a framework for creating and implementing networking standards, devices, and internetworking schemes. It explains the networking from a modular perspective, making it easier to understand and troubleshoot.
Seven layers of the OSI Model
The OSI model has seven different layers, which are divided into two groups. The following table lists all the layers with their names and numbers.

Let’s understand each layer in detail.
This tutorial is the second part of the article " Networking reference models explained in detail with examples. ". Other parts of this article are the following.
This tutorial is the first part of the article. It summarizes why the OSI model was created and what advantages it has.
This tutorial is the third part of the article. It compares the OSI reference model with the TCP/IP model and lists the similarities and differences between both.
This tutorial is the fourth part of the article. It explains the five layers of the TCP/IP model in detail.
This tutorial is the fifth part of the article. It explains how data is encapsulated and de-encapsulated when it passes through the layers.
The Application Layer
This is the last and topmost layer of the OSI model. This layer provides an interface between the local system and the application program running on the network. If an application wants to use the resources available on the remote system, it interacts with this layer. Then, this layer provides the protocols and services that the application needs to access those resources.
There are two types of application programs: Network-aware and Network-unaware . An application program is considered a Network-aware application if it can make any type of network request. If an application program cannot make any type of network request, it is considered a Network-unaware program.
Network-aware programs are further divided into two types.
Programs that are mainly built to work on a local system. This type of program occasionally accesses the network for particular reasons such as updates, documentation, and troubleshooting. MS-Word, Adobe-Photoshop, and VLC Player are examples of this type of program.
Programs that are mainly built to work with a remote system. This type of program provides a platform to access resources available on a remote system. This type of program only works if the system is connected to the network. SSH, FTP, and TFTP are examples of this type of program.
The Application layer describes only the programs which fall in the second type. But it doesn’t mean that the first type of programs can’t take the advantage of the Application layer. It simply means that they are not documented in the Application layer. But if required, they can also connect to the network through the Application layer.
The Top layer of the OSI model is the application layer. It provides the protocols and services that are required by the network-aware applications to connect to the network. FTP, TFTP, POP3, SMTP, and HTTP are examples of standards and protocols used in this layer.
The Presentation Layer
The sixth layer of the OSI model is the Presentation layer. Applications running on the local system may or may not understand the format that is used to transmit the data over the network. The presentation layer works as a translator. When receiving data from the Application layer, it converts that data in such a format that can be sent over the network. When receiving data from the Session layer, it reconverts the data in such a format that the application, which will use it, can understand.
Conversion, compression, and encryption are the main functions that the Presentation layer performs on the sending computer while on the receiving computer these functions are reconversion, decompression, and decryption. ASCII, BMP, GIF, JPEG, WAV, AVI, and MPEG are examples of standards and protocols that work in this layer.
The Session Layer
The session layer is the fifth layer of the OSI model. It is responsible for setting up, managing, and dismantling sessions between presentation layer entities and providing dialogs between computers.
When an application makes a network request, this layer checks whether the requested resource is available on the local system or on a remote system. If the requested resource is available on a remote system, it tests whether a network connection to access that resource is available or not. If a network connection is not available, it sends an error message back to the application informing that the connection is not available.
If a network connection is available, it establishes a session with the remote system. For each request, it uses a separate session. This allows multiple applications to send or receive data simultaneously. When data transmission is completed, it terminates the session.
The session layer is responsible for establishing, managing, and terminating communications between two computers. RPCs and NFS are examples of the session layer.
The Transport Layer
The transport layer is the fourth layer of the OSI model. It provides the following functionalities: -
Segmentation
On the sending computer, it breaks the data stream into smaller pieces. Each piece is known as a segment and the process of breaking the data stream into smaller pieces is known as the segmentation . On the receiving computer, it joins all segments to recreate the original data stream.
Data transportation
This layer establishes a logical connection between the sending system and receiving system and uses that connection to provide end-to-end data transportation. This process uses two protocols: TCP and UDP.
The TCP protocol is used for reliable data transportation. TCP is a connection-oriented protocol. UDP protocol is used for unreliable data transportation. UDP is a connection-less protocol.
The main difference between a connection-less and connection-oriented protocol is that a connection-oriented protocol provides reliable data delivery. For reliable data delivery, it uses several mechanisms such as the three-way handshake process, acknowledgments, sequencing, and flow control.
Multiplexing
Through the use of port numbers, this layer also provides connection multiplexing. Connection multiplexing allows multiple applications to send and receive data simultaneously.
The main functionalities of the Transport layer are segmentation, data transportation, and connection multiplexing. For data transportation, it uses TCP and UDP protocols. TCP is a connection-oriented protocol. It provides reliable data delivery.
The Network Layer
The third layer of the OSI model is the Network Layer. This layer takes the data segment from the Transport layer and adds a logical address to it. A logical address has two components; network partition and host partition. The Network partition is used to group networking components while the host partition is used to uniquely identify a system on the network. A logical address is known as the IP address. Once the logical address and other related information are added to the segment , it becomes the packet .
This layer decides whether the packet is intended for the local system or a remote system. It also specifies the standards and protocols which are used to move data packets over networks.
To move data packets between two different networks, a device known as the router is used. Routers use the logical address to make the routing decision. Routing is the process of forwarding data packets to their destination.
Defining logical addresses and finding the best path to reach the destination address are the main functions of this layer. Routers work in this layer. Routing also takes place in this layer. IP, IPX, and AppleTalk are examples of this layer.
The Data Link Layer
The Data Link Layer is the second layer of the OSI model. This layer defines how networking components access the media and what transmission methods they use. This layer has two sub-layers: MAC and LLC.
MAC (Media Access Control)
This sub-layer defines how the data packets are placed in media. It also provides physical addressing. The physical address is known as the MAC address. Unlike logical addresses that need to be configured, physical addresses are pre-configured in NIC. The MAC address is used to uniquely identify a host in the local network.
LLC (Logical Link Control)
This sub-layer identifies the network layer protocol. On the sending computer, it encapsulates the information of the Network Layer protocol in the LLC header from which the Data Link layer receives the data packet. On the receiving computer, it checks the LLC header to get the information about the network layer protocol. This way, a data packet is always delivered to the same network layer protocol from which it was sent.
Defining physical addresses, finding hosts in the local network, specifying standards and methods to access the media are the primary functions of this layer. Switching takes place in this layer. Switches and Bridges work in this layer. HDLC, PPP, and Frame Relay are examples of this layer.
The Physical Layer
The Physical Layer is the first layer of the OSI model. This layer specifies the standards for devices, media, and technologies that are used in moving the data across the network such as:-
- Type of cable used in connecting the devices
- Patterns of pins used in both sides of the cable
- Type of interface-card used in the networking device
- Type of connector used to connect the cable with the network interface
- Encoding of digital signals received from the Data Link layer based on the attached media type such as electrical for copper, light for fiber, or a radio wave for wireless.
On the sending computer, it converts digital signals received from the Data Link layer, into analog signals and loads them on the physical media. On the receiving computer, it picks analog signals from the media and converts them into digital signals, and transfers them to the Data Link layer for further processing.
The Physical Layer mainly defines standards for media and devices that are used to move data across the network. 10BaseT, 10Base100, CSU/DSU, DCE, and DTE are examples of the standards used in this layer.
That’s all for this tutorial. In the next part of this article, we will compare the OSI model with the TCP/IP model and explains the similarities and differences between both models. If you like this tutorial, please don’t forget to share it with friends.
By ComputerNetworkingNotes Updated on 2024-01-25 05:30:01 IST
ComputerNetworkingNotes CCNA Study Guide OSI Seven Layers Model Explained with Examples
We do not accept any kind of Guest Post. Except Guest post submission, for any other query (such as adverting opportunity, product advertisement, feedback, suggestion, error reporting and technical issue) or simply just say to hello mail us [email protected]

What is the OSI Model? 7 layers explained in detail
The Open Systems Interconnection (OSI) model is a framework in network communication that simplifies complex network interactions into a structured format.
What Is the OSI Model?
The Open Systems Interconnection model is a framework in network communication designed to simplify complex network interactions into a structured format. This architecture has seven layers, each of which serves a specific function. All seven layers work together to create a robust and efficient network communication system.
Each of its seven layers has a distinct role, ensuring efficient data transfer from one device to another . The OSI model is essential for understanding how data is transmitted in a network and is also a practical guide for network protocol design and problem solving.
learn more about cybersecurity An Introduction to Microsegmentation in Network Security
The OSI model, developed by the International Organization for Standardization , outlines the essential functions of networking and telecommunications systems for practical application. It plays a crucial role in telecommunications, where vendors use it to define the features and capabilities of their products and services.
This approach allows for a detailed explanation of different aspects of network communication, including transport protocols, addressing schemes and data packaging methods. As a result, the OSI model resolves the complexities of network communication and fosters a more integrated and coherent digital world .
The 7 Layers of the OSI Model
Each layer of the OSI model serves a specific function, yet they work in harmony to create a robust and efficient network communication system. Understanding these layers provides valuable insights into the complexities of network design and operation, showcasing the intricate nature of modern digital communication.
Layer 7: Application Layer
Functionality: The Application Layer is the closest to the end user. It facilitates user interaction with networked systems, providing interfaces and protocols for web browsers, email clients and other applications.
Key protocols: Protocols like HTTP, FTP and SMTP operate at this layer, enabling services such as web browsing, file transfers and email communications.
Layer 6: Presentation Layer
Role: The Presentation Layer acts as a translator, converting data formats from the application layer into a network-compatible format and vice versa. It ensures that data sent from one system is readable by another.
Data formatting: This layer is responsible for data encryption and compression, playing a significant role in maintaining data privacy and efficient transmission.
Layer 5: Session Layer
Managing sessions: It establishes, manages and terminates sessions between applications. This layer ensures that sessions are maintained for the duration of the communication.
Coordination: The Session Layer coordinates communication between systems, managing dialogues and synchronizing data exchange.
Layer 4: Transport Layer
Data segmentation and control: The Transport Layer is crucial for segmenting data into smaller packets. It ensures end-to-end data integrity and delivery, managing flow control, error correction and sequencing.
Protocols: TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) are key protocols in this layer, differing in their approach to data transmission.
Layer 3: Network Layer
Routing and addressing: This layer is responsible for logical addressing and routing data packets across different networks. It determines the best path for data to travel from source to destination.
Internet protocol: The Internet Protocol (IP), fundamental for internet data exchange, operates at this layer.
Layer 2: Data Link Layer
Framing and MAC addressing: The Data Link Layer frames data into packets. It handles physical addressing through MAC addresses, ensuring that data is directed to the correct hardware.
Error detection: This layer is also involved in error detection and handling, improving overall data transmission reliability.
Layer 1: Physical Layer
Physical transmission: The Physical Layer deals with the physical aspects of data transmission, including cable types, electrical signals and data rates.
Hardware components: It involves hardware components like cables, switches and network interface cards, forming the foundation of network communication.
How Data Flows in the OSI Model
Understanding this data flow process is crucial for professionals, as it aids in diagnosing and troubleshooting network issues, designing efficient network solutions and ensuring robust data security and management.
Encapsulation Process
When data is sent, it begins at the Application Layer and moves down through the layers. At each stage, it is encapsulated with the necessary headers, trailers, and other control information relevant to that layer. For instance, at the Transport Layer, data is segmented and encapsulated with port numbers, while at the Network Layer, IP addresses are added.
Each layer plays a role in preparing the data for transmission. The Presentation Layer may encrypt the data for security, while the Data Link Layer ensures it is formatted into frames suitable for physical transmission.
Data Transmission Across the Network
The Physical Layer transmits the raw bits over a physical medium, such as a cable or wireless network. This transmission is the actual movement of data across the network. In cases where data must move across different networks, the Network Layer’s routing functionalities become crucial. It ensures that data packets find the most efficient path to their destination.
Decapsulation Process
Upon reaching the destination, the data moves up the OSI model, with each layer removing its respective encapsulation. The Data Link Layer, for instance, removes framing, and the Transport Layer checks for transmission errors and reassembles the data segments. Once the data reaches the Application Layer, it is in its original format and ready to be used by the receiving application, whether it’s an email client, a web browser or any other networked software.

Seamless Data Flow
The OSI model ensures that each layer only communicates with its immediate upper and lower layers, creating a seamless flow. This layered approach means changes in one layer’s protocols or functionalities can occur without disrupting the entire network.
OSI Model Advantages
The OSI model is a cornerstone in network architecture for several reasons:
Simplification of network design
The OSI model’s layered approach breaks down complex network processes, making design and operation more manageable. Each layer focuses on a specific aspect of communication, allowing for independent development and easier troubleshooting.
Standardization and interoperability
It establishes universal standards for network communication, enabling different technologies to interact seamlessly. This interoperability is crucial for the efficient functioning of diverse network devices and applications.
Flexibility and Scalability
Adaptable to technological advancements, the OSI model allows individual layers to evolve without overhauling the entire system. This scalability makes it suitable for various network sizes and types.
Enhanced Security
Security measures are integrated at multiple layers, providing a robust defense against threats. Each layer can address specific security concerns, leading to comprehensive network protection.
Real-World Applications of the OSI Model
The OSI model’s influence extends well beyond theoretical concepts, playing a crucial role in various practical aspects of networking:
Network Design and Protocol Development
Network professionals use the OSI model as a blueprint for structuring and developing robust networks. It guides the creation of new protocols, ensuring seamless integration and functionality across different network layers.
Efficient Troubleshooting and Management
In troubleshooting, the OSI model provides a systematic approach for identifying issues, from physical connectivity to application-level errors. It also aids in network maintenance and performance optimization, addressing each layer to enhance overall efficiency.
Cybersecurity Strategy
The model is foundational in crafting layered security strategies . By implementing security measures at different layers, it offers comprehensive protection against various cyber threats. Understanding the OSI layers is key in detecting and mitigating attacks targeting specific network segments.
Educational and Training Tool
It serves as an essential framework in networking education, helping students and professionals alike understand complex network operations. The OSI model is a cornerstone in training programs , emphasizing the intricacies of network architecture and security.
safety first When and How to Run a Phishing Simulation
OSI Model vs. TCP/IP Model
While the OSI model offers a detailed conceptual framework, the TCP/IP model is recognized for its practical application in today’s internet-driven world.
Structural Differences
OSI model : Introduced as a comprehensive, protocol-independent framework, the OSI model details seven distinct layers, offering a more granular approach to network communication.
TCP/IP model : Developed earlier by the U.S. Department of Defense, the TCP/IP model consists of four layers (Application, Transport, Internet and Network Access), combining certain OSI layers.
Theoretical vs. Practical Approach
OSI model : Developed as a theoretical and universal networking model, it’s used more for educational purposes to explain how networks operate.
TCP/IP model : This model is designed around specific standard protocols, focusing on solving practical communication issues. It leaves sequencing and acknowledgment functions to the transport layer, differing from the OSI approach.
Adoption and Use
OSI model: While not widely implemented in its entirety, the OSI model’s clear layer separation is influential in protocol design and network education; simpler applications in the OSI framework may not utilize all seven layers, with only the first three layers (Physical, Data Link, and Network) being mandatory for basic data communication.
TCP/IP model : The dominant model used in most network architectures today, especially in internet-related communications. In TCP/IP, most applications engage all layers for communication.
Frequently Asked Questions
Why is the osi model important.
The OSI model is crucial for standardizing network communication and ensuring interoperability between various devices and systems. It simplifies network design and troubleshooting and serves as a fundamental educational tool in networking.
What are the 7 layers of the OSI model?
Layer 1: Physical Layer — Transmits raw data.
Layer 2: Data Link Layer — Manages direct links and framing.
Layer 3: Network Layer — Handles addressing and routing.
Layer 4: Transport Layer — Ensures reliable data transfer.
Layer 5: Session Layer — Manages connections.
Layer 6: Presentation Layer — Translates data formats.
Layer 7: Application Layer — Interfaces with applications.
Recent Expert Contributors Articles

PrepBytes Blog
ONE-STOP RESOURCE FOR EVERYTHING RELATED TO CODING
Sign in to your account
Forgot your password?
Login via OTP
We will send you an one time password on your mobile number
An OTP has been sent to your mobile number please verify it below
Register with PrepBytes
Presentation layer in osi model.
Last Updated on March 7, 2024 by Abhishek Sharma

The OSI (Open Systems Interconnection) model is a conceptual framework used to understand the functions of a telecommunication or computing system. It consists of seven layers, each responsible for specific tasks. The sixth layer, known as the Presentation Layer, plays a crucial role in ensuring that data exchanged between systems is readable and usable. Let’s explore the functions and importance of the Presentation Layer in the OSI model.
What is Presentation Layer in OSI Model?
The Presentation Layer, the sixth layer of the OSI (Open Systems Interconnection) model, is responsible for ensuring that data exchanged between systems is in a format that can be interpreted and used by the receiving system. It performs various functions, including data translation, encryption, compression, and formatting, to facilitate efficient and secure communication between networked devices.
Functions of the Presentation Layer
Below are some of the functions of the Presentation Layer in OSI Model:
- Data Translation: The Presentation Layer translates data from the format used by the application layer into a format that can be transmitted over the network. This includes encoding, compression, and encryption.
- Data Formatting: It ensures that data is formatted according to the specifications of the application layer. This includes converting between different character sets, such as ASCII and Unicode.
- Data Compression: The Presentation Layer compresses data to reduce the amount of bandwidth required for transmission, improving network efficiency.
- Data Encryption: It encrypts data to ensure that it remains secure during transmission, protecting it from unauthorized access.
- Data Syntax: The Presentation Layer defines the syntax for data representation, ensuring that both the sender and receiver understand the structure of the data being exchanged.
Importance of the Presentation Layer
Importance of Presentation Layer are:
- Data Integrity: By ensuring that data is formatted correctly and encrypted, the Presentation Layer helps maintain the integrity of data during transmission.
- Interoperability: The Presentation Layer enables different systems to communicate with each other by ensuring that data is translated into a common format that both systems understand.
- Efficiency: Data compression reduces the amount of data that needs to be transmitted, improving network efficiency and reducing bandwidth requirements.
- Security: Encryption provided by the Presentation Layer ensures that data remains secure and protected from unauthorized access.
Conclusion The Presentation Layer is a crucial component of the OSI model, responsible for ensuring that data exchanged between systems is in a format that can be understood and used. By performing functions such as data translation, formatting, compression, and encryption, the Presentation Layer plays a vital role in maintaining data integrity, facilitating interoperability, and ensuring the security of data during transmission.
FAQs related to Presentation Layer in OSI Model
Here are some of the FAQs related to Presentation Layer in OSI Model:
Q1: What is the role of the Presentation Layer in the OSI model? The Presentation Layer ensures that data exchanged between systems is in a usable format, performing functions such as data translation, encryption, compression, and formatting.
Q2: How does the Presentation Layer ensure data security? The Presentation Layer encrypts data before transmission, making it unreadable to unauthorized parties, thus ensuring data security.
Q3: Why is data compression important in the Presentation Layer? Data compression reduces the size of data packets, leading to faster transmission speeds and optimized bandwidth usage, which is crucial in high-traffic networks.
Q4: How does the Presentation Layer facilitate interoperability between systems? By translating data into a common format that both sender and receiver understand, the Presentation Layer enables different systems to communicate with each other seamlessly.
Q5: Can the Presentation Layer be bypassed in data transmission? While it is possible to bypass the Presentation Layer in some cases, doing so can lead to compatibility issues between systems and is not recommended.
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *
Save my name, email, and website in this browser for the next time I comment.
- Linked List
- Segment Tree
- Backtracking
- Dynamic Programming
- Greedy Algorithm
- Operating System
- Company Placement
- Interview Tips
- General Interview Questions
- Data Structure
- Other Topics
- Computational Geometry
- Game Theory
Related Post
Quantum cryptography, introduction to sniffers, multiplexing and demultiplexing in transport layer, transport layer responsibilities, tacacs+ and radius.
- Editor's Choice: Tech Gifts for Mom
- New! iPad Air 6 Details
The Layers of the OSI Model Illustrated
Each layer explained
- Massachusetts Institute of Technology
- University of Illinois
:max_bytes(150000):strip_icc():format(webp)/image-5e6611aebe974bb7886a24b5070c834f.jpg)
- The Wireless Connection
- Routers & Firewalls
- Network Hubs
- Installing & Upgrading
- Wi-Fi & Wireless
The Open Systems Interconnection (OSI) model defines a networking framework to implement protocols in layers, with control passed from one layer to the next. It is primarily used today as a teaching tool. It conceptually divides computer network architecture into 7 layers in a logical progression.
The lower layers deal with electrical signals, chunks of binary data , and routing of these data across networks. Higher levels cover network requests and responses, representation of data, and network protocols, as seen from a user's point of view.
The OSI model was originally conceived as a standard architecture for building network systems, and many popular network technologies today reflect the layered design of OSI.
Physical Layer
At Layer 1, the Physical layer of the OSI model is responsible for the ultimate transmission of digital data bits from the Physical layer of the sending (source) device over network communications media to the Physical layer of the receiving (destination) device.
Examples of layer 1 technologies include Ethernet cables and hubs . Also, hubs and other repeaters are standard network devices that function at the Physical layer, as are cable connectors.
At the Physical layer, data is transmitted using the type of signaling supported by the physical medium: electric voltages, radio frequencies, or pulses of infrared or ordinary light.
Data Link Layer
When obtaining data from the Physical layer, the Data Link layer checks for physical transmission errors and packages bits into data frames. The Data Link layer also manages physical addressing schemes such as MAC addresses for Ethernet networks, controlling access of network devices to the physical medium.
Because the Data Link layer is the most complex layer in the OSI model, it is often divided into two parts: the Media Access Control sub-layer and the Logical Link Control sub-layer.
Network Layer
The Network layer adds the concept of routing above the Data Link layer. When data arrives at the Network layer, the source and destination addresses contained inside each frame are examined to determine if the data has reached its final destination. If the data has reached the final destination, layer 3 formats the data into packets delivered to the Transport layer. Otherwise, the Network layer updates the destination address and pushes the frame down to the lower layers.
To support routing, the Network layer maintains logical addresses such as IP addresses for devices on the network. The Network layer also manages the mapping between these logical addresses and physical addresses. In IPv4 networking, this mapping is accomplished through the Address Resolution Protocol (ARP); IPv6 uses Neighbor Discovery Protocol (NDP).
Transport Layer
The Transport Layer delivers data across network connections. TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) are the most common examples of Transport Layer 4 network protocols. Different transport protocols may support a range of optional capabilities, including error recovery, flow control, and support for re-transmission.
Session Layer
The Session Layer manages the sequence and flow of events that initiate and tear down network connections. At layer 5, it is built to support multiple types of connections that can be created dynamically and run over individual networks.
Presentation Layer
The Presentation layer has the simplest function of any piece of the OSI model. At layer 6, it handles syntax processing of message data such as format conversions and encryption/decryption needed to support the Application layer above it.
Application Layer
The Application layer supplies network services to end-user applications. Network services are protocols that work with the user's data. For example, in a web browser application, the Application layer protocol HTTP packages the data needed to send and receive web page content. This layer 7 provides data to (and obtains data from) the Presentation layer.
Get the Latest Tech News Delivered Every Day
- Common Questions and Answers on the OSI Network Model
- A Guide to X.25 in Computer Networking
- OSI Model Reference Guide
- Wireless Access Point vs. Wireless Application Protocol
- Visual Index of Computer Networking Topics
- Here's Why Your Network Might Need a Layer 3 Switch
- Understanding Transmission Control Protocol/Internet Protocol (TCP/IP)
- What Is PPTP: Point-to-Point Tunneling Protocol
- How Do Computer Network Protocols Work?
- Beginner's Guide to Asynchronous Transfer Mode (ATM)
- ARP (Address Resolution Protocol) and Your Computer Network
- What Is a Virtual LAN (VLAN)?
- Use a Bridge to Expand Your Local Network
- A Short Guide on Networking Fundamentals
- What Are Network Protocols?
- What Is a Switch?
The Cisco Learning Network
Osi model reference chart, aug 19, 2021 • knowledge, information.
Those who start towards the path of CCNA understand the OSI model as a core component that continues throughout the rest of the Cisco certification tracks.
The Open Systems Interconnection model (OSI model) is a seven layer conceptual model that characterizes and standardizes the communication functions of a telecommunication or computing system.
The physical layer , which is the bottom layer of the OSI model, is concerned with the transmission and reception of the unstructured raw bit stream over a physical medium. It describes the electrical/optical, mechanical, and functional interfaces to the physical medium, and it carries the signals for all of the higher layers.
The data link layer provides error-free transfer of data frames from one node to another over the physical layer, allowing layers above it to assume virtually error-free transmission over the link.
The network layer controls the operation of the subnet, deciding which physical path the data should take based on network conditions, priority of service, and other factors.
The transport layer ensures that messages are delivered error-free, in sequence, and with no losses or duplications.
The session layer allows session establishment between processes running on different stations.
The presentation layer formats the data to be presented to the application layer. It can be viewed as the translator for the network. This layer may translate data from a format used by the application layer into a common format at the sending station, then translate the common format to a format known by the application layer at the receiving station.
The application layer serves as the window for users and application processes to access network services.
The Cisco Learning Network has developed an OSI model chart to help aid in your learning. This chart organizes and describes the seven layers, providing examples in the form of protocols and devices, as well as in relation to the DOD TCP/IP Model.

Article Details
Aug 22, 2021 103 KB pdf

Rolitto1976
Great summarized chart.

david.wadsworth80
Nice chart, though I would update it to include the TCP/IP 5 Layer model as well. For anyone looking at the OSI model, the top 3 layers (layer 7, 6, 5) are mapped to the Application layer for the TCP/IP model, with the lower layers (Layer 4 - Layer 1) are mapped 1:1, with the Data Link Layer mapped as the Network Interface Layer.

Thank you for sharing

Instant Like! Never thought that in here i could find so much Information for the self educated People.
Matt Saunders
Glad you like!

jdewitt2011
Very good information and definitely added value that we can download the OSI Model Chart for studying purposes. Even though the Transport layer is missing.
Thank you for sharing all this information with us.
You're welcome Nicole!
I appreciate you letting me know that the transport layer has now been added to the summary page.

akhilkamalakaran
A good one, thanks for share

This looks awesome!
Related Articles
- Number of Views 582
- Number of Views 4.28K
- Number of Views 16.75K
Trending Articles
- Cisco Packet Tracer: Software de Simulación para Redes
- 200-301 CCNA Study Materials
- Packet Tracer Labs
If you encounter a technical issue on the site, please open a support case .
Communities: Chinese | Japanese | Korean
Cisco.com © Copyright 2024 Cisco, Inc. All Rights Reserved. Privacy Statement Terms & Conditions Cookie Policy Trademarks
- Artificial Intelligence
- Generative AI
- Cloud Computing
- CPUs and Processors
- Data Center
- Edge Computing
- Enterprise Storage
- Virtualization
- Internet of Things
- Network Management Software
- Network Security
- Enterprise Buyer’s Guides
- United States
- Newsletters
- Foundry Careers
- Terms of Service
- Privacy Policy
- Cookie Policy
- Copyright Notice
- Member Preferences
- About AdChoices
- E-commerce Links
- Your California Privacy Rights
Our Network
- Computerworld

The OSI model explained and how to easily remember its 7 layers
A tutorial on the open systems interconnection networking reference model and tips on and how to memorize the seven layers.

The Open Systems Interconnect (OSI) model is a conceptual framework that describes networking or telecommunications systems as seven layers, each with its own function.
The layers help network pros visualize what is going on within their networks and can help network managers narrow down problems (is it a physical issue or something with the application?), as well as computer programmers (when developing an application, which other layers does it need to work with?). Tech vendors selling new products will often refer to the OSI model to help customers understand which layer their products work with or whether it works “across the stack”.
The 7 layers of the OSI model
The layers are: Layer 1—Physical; Layer 2—Data Link; Layer 3—Network; Layer 4—Transport; Layer 5—Session; Layer 6—Presentation; Layer 7—Application.
It wasn’t always this way. Conceived in the 1970s when computer networking was taking off, two separate models were merged in 1983 and published in 1984 to create the OSI model that most people are familiar with today. Most descriptions of the OSI model go from top to bottom, with the numbers going from Layer 7 down to Layer 1. The layers, and what they represent, are as follows:
Layer 7 – Application
The Application Layer in the OSI model is the layer that is the “closest to the end user”. It receives information directly from users and displays incoming data to the user. Oddly enough, applications themselves do not reside at the application layer. Instead the layer facilitates communication through lower layers in order to establish connections with applications at the other end. Web browsers (Google Chrome, Firefox, Safari, etc.) TelNet, and FTP, are examples of communications that rely on Layer 7.
Layer 6 – Presentation
The Presentation Layer represents the area that is independent of data representation at the application layer. In general, it represents the preparation or translation of application format to network format, or from network formatting to application format. In other words, the layer “presents” data for the application or the network. A good example of this is encryption and decryption of data for secure transmission; this happens at Layer 6.
Layer 5 – Session
When two computers or other networked devices need to speak with one another, a session needs to be created, and this is done at the Session Layer . Functions at this layer involve setup, coordination (how long should a system wait for a response, for example) and termination between the applications at each end of the session.
Layer 4 – Transport
The Transport Layer deals with the coordination of the data transfer between end systems and hosts. How much data to send, at what rate, where it goes, etc. The best known example of the Transport Layer is the Transmission Control Protocol (TCP), which is built on top of the Internet Protocol (IP), commonly known as TCP/IP. TCP and UDP port numbers work at Layer 4, while IP addresses work at Layer 3, the Network Layer.
Layer 3 – Network
Here at the Network Layer is where you’ll find most of the router functionality that most networking professionals care about and love. In its most basic sense, this layer is responsible for packet forwarding, including routing through different routers . You might know that your Boston computer wants to connect to a server in California, but there are millions of different paths to take. Routers at this layer help do this efficiently.
Layer 2 – Data Link
The Data Link Layer provides node-to-node data transfer (between two directly connected nodes), and also handles error correction from the physical layer. Two sublayers exist here as well–the Media Access Control (MAC) layer and the Logical Link Control (LLC) layer. In the networking world, most switches operate at Layer 2. But it’s not that simple. Some switches also operate at Layer 3 in order to support virtual LANs that may span more than one switch subnet, which requires routing capabilities.
Layer 1 – Physical
At the bottom of our OSI model we have the Physical Layer, which represents the electrical and physical representation of the system. This can include everything from the cable type, radio frequency link (as in a Wi-Fi network), as well as the layout of pins, voltages, and other physical requirements. When a networking problem occurs, many networking pros go right to the physical layer to check that all of the cables are properly connected and that the power plug hasn’t been pulled from the router, switch or computer, for example.
Why you need to know the 7 OSI layers
Most people in IT will likely need to know about the different layers when they’re going for their certifications, much like a civics student needs to learn about the three branches of the US government. After that, you hear about the OSI model when vendors are making pitches about which layers their products work with.
In a Quora post asking about the purpose of the OSI model, Vikram Kumar answered this way:
“The purpose of the OSI reference model is to guide vendors and developers so the digital communication products and software programs they create will interoperate, and to facilitate clear comparisons among communications tools.”
While some people may argue that the OSI model is obsolete (due to its conceptual nature) and less important than the four layers of the TCP/IP model, Kumar says that “it is difficult to read about networking technology today without seeing references to the OSI model and its layers, because the model’s structure helps to frame discussions of protocols and contrast various technologies.”
If you can understand the OSI model and its layers, you can also then understand which protocols and devices can interoperate with each other when new technologies are developed and explained.
The OSI model remains relevant
In a post on GeeksforGeeks, contributor Vabhav Bilotia argues several reasons why the OSI model remains relevant, especially when it comes to security and determining where technical risks and vulnerabilities may exist.
For example, by understanding the different layers, enterprise security teams can identify and classify physical access, where the data is sitting, and provide an inventory of the applications that employees use to access data and resources.
“Knowing where the majority of your company’s data is held, whether on-premises or in cloud services, will help define your information security policy,” writes Bilotia. “You can invest in the correct solutions that provide you data visibility within the proper OSI layers once you have this knowledge.”
In addition, the OSI model can be used to understand cloud infrastructure migrations, particularly when it comes to securing data within the cloud.
And because the model has been around for so long and understood by so many, the uniform vocabulary and terms helps networking professionals understand quickly about the components of the networking system “While this paradigm is not directly implemented in today’s TCP/IP networks, it is a useful conceptual model for relating multiple technologies to one another and implementing the appropriate technology in the appropriate way,” Bilotia writes. We couldn’t agree more.
How to remember the OSI Model 7 layers – 8 mnemonic tricks
If you need to memorize the layers for a college or certification test, here are a few sentences to help remember them in order. The first letter of each word is the same as the first letter an OSI layer.
From Application to Physical (Layer 7 to Layer 1):
- All People Seem To Need Data Processing
- All Pros Search Top Notch Donut Places
- A Penguin Said That Nobody Drinks Pepsi
- A Priest Saw Two Nuns Doing Pushups
From Physical to Application (Layer 1 to Layer 7):
- Please Do Not Throw Sausage Pizza Away
- Pew! Dead Ninja Turtles Smell Particularly Awful
- People Don’t Need To See Paula Abdul
- Pete Doesn’t Need To Sell Pickles Anymore
Keith Shaw was a Network World editor and the writer of the Cool Tools column. He is now a freelance writer and editor from Worcester, Mass.
Related content
Red hat unveils image mode for its linux distro, insecure protocols leave networks vulnerable: report, what is a digital twin and why is it important to iot, 2024 global network outage report and internet health check, newsletter promo module test.

The first gadget Keith Shaw ever wanted was the Merlin, a red plastic toy that beeped and played Tic-Tac-Toe and various other games. A child of the '70s and teenager of the '80s, Shaw has been a fan of computers, technology and video games right from the start. He won an award in 8th grade for programming a game on the school's only computer, and saved his allowance to buy an Atari 2600.
Shaw has a bachelor's degree in newspaper journalism from Syracuse University and has worked at a variety of newspapers in New York, Florida and Massachusetts, as well as Computerworld and Network World. He won an award from the American Society of Business Publication Editors for a 2003 article on anti-spam testing, and a Gold Award in their 2010 Digital Awards Competition for the "ABCs of IT" video series.
Shaw is also the co-creator of taquitos.net , the crunchiest site on the InterWeb, which has taste-tested and reviewed more than 4,000 varieties of snack foods.
More from this author
What is a virtual machine, and why are they so useful, what is a network switch and how does it work, what is zero trust network access, what is sd-wan, and what does it mean for networking, security, cloud, most popular authors.

- Elizabeth Montalbano
Show me more
Google cloud issue blamed for unisuper week-long service disruption.

IBM Power server targets AI workloads at the edge

HPE Aruba looks to fight AI threats with AI weapons

Has the hype around ‘Internet of Things’ paid off? | Ep. 145

Episode 1: Understanding Cisco’s Converged SDN Transport

Episode 2: Pluggable Optics and the Internet for the Future

Has the hype around ‘Internet of Things’ paid off?

Are unused IPv4 addresses a secret gold mine?

Preparing for a 6G wireless world: Exciting changes coming to the wireless industry


- Data Structure
- Coding Problems
- C Interview Programs
- C++ Aptitude
- Java Aptitude
- C# Aptitude
- PHP Aptitude
- Linux Aptitude
- DBMS Aptitude
- Networking Aptitude
- AI Aptitude
- MIS Executive
- Web Technologie MCQs
- CS Subjects MCQs
- Databases MCQs
- Programming MCQs
- Testing Software MCQs
- Digital Mktg Subjects MCQs
- Cloud Computing S/W MCQs
- Engineering Subjects MCQs
- Commerce MCQs
- More MCQs...
- Machine Learning/AI
- Operating System
- Computer Network
- Software Engineering
- Discrete Mathematics
- Digital Electronics
- Data Mining
- Embedded Systems
- Cryptography
- CS Fundamental
- More Tutorials...
- Tech Articles
- Code Examples
- Programmer's Calculator
- XML Sitemap Generator
- Tools & Generators
Computer Network Tutorial
- Computer Network - Home
- Computer Network - Overview
- Computer Network - Applications
- Computer Network - TCP/IP
- Computer Network - OSI Model
- Computer Network - Transport, Network, & Application Layers
- Computer Network - Network Protocols & Network Software
- Computer Network - TopologiesTypes
- Computer Network - Hub
- Computer Network - Routing
- Computer Network - Routers
- Computer Network - Dynamic Routing Protocols
- Computer Network - Router
- Computer Network - Populating a Routing Table
- Computer Network - Switches
- Computer Network - Layer 2 Switching
- Computer Network - Configure Cisco Switch
- Computer Network - ICMP
- Computer Network - ICMP Messages
- Computer Network - Addressing
- Computer Network - Classless Addressing
- Computer Network - IPV4 Addressing
- Computer Network - IPV6 Addressing
- Computer Network - Logical Addressing, Notations
- Computer Network - Classful & Classless Addressing
- Computer Network - Subnetting & Supernetting
- Computer Network - Network Address Translation
- Computer Network - FLSM & VLSM
- Computer Network - Line Configuration
- Transmission Computer Network - Modes
- Computer Network - Data Link Layer
- Computer Network - Physical Layer
- Computer Network - Network Layer
- Computer Network - Session Layer
- Computer Network - Transport Layer
- Computer Network - Application Layer
- Computer Network - Presentation Layer
- Computer Network - Coaxial Cable
- Computer Network - Optical Fiber
- Computer Network - Unguided Transmission Media
- Computer Network - Virtual LAN (VLAN)
- Computer Network - VSAN
- Computer Network - Multiple Access Protocol
- Computer Network - Random Access methods
- Computer Network - Aloha Network
- Computer Network - CSMA
- Computer Network - FDMA & TDMA
- Computer Network - CDMA
- Computer Network - Ethernet Technology
- Computer Network - Types of Network Topology
- Computer Network - Data Transmission
- Computer Network - Switching Techniques
- Computer Network - Transmission Impairment
- Computer Network - Synchronous & Asynchronous Transmission
- Computer Network - Intent-Based Networking
- Computer Network - Software-Defined Networking
- Computer Network - Wireless Personal Area Network
- Computer Network - Wireless Wide Area Network
- Computer Network - P2P File Sharing
- Computer Network - Packet Switching
- Computer Network - PGP - Authentication & Confidentiality
- Computer Network - PGP - Encryption & Compression
- Computer Network - Phishing Attacks
- Computer Network - ICMP Ping
- Computer Network - Pipelining in Packet Switching
- Computer Network - Plaintext Vs. Cleartext Encryption
- Computer Network - Platform as a Service (PaaS)
- Computer Network - GPRS Architecture
- Computer Network - Identify & Prevent Phishing & Pharming
- Computer Network - Change MAC Address
- Computer Network - Network Administrator Vs. Network Engineer
Difference B/W Articles
- Computer Network - Phishing & Pharming
- Computer Network - Ping Vs. Traceroute
- Computer Network - Network Vs. System Administrator
- Computer Network - Network & Application Layer Protocols
- Computer Network - Network Security Vs. Network Administration
- Computer Network - Network Vs. Internet
- Computer Network - PDH Vs. SDH
- Computer Network - PCI Vs. PCI express
- Computer Network - PCI-E Vs. PCI-X
- Computer Network - OT Vs. IT Networks
Computer Network Practice
- Computer Network - MCQs
- Computer Network - Aptitude Questions
Home » Computer Network
Presentation Layer: What It Is, Design Issues, Functionalities
Description and Functions of Presentation Layer in the OSI model: In this tutorial, we are going to learn what the Presentation layer is and the Functions of the Presentation Layer in the OSI model in Computer Networking. We will also discuss the Design issues with the Presentation Layer and the working of the Presentation Layer with the help of its diagram. By Monika Jha Last updated : May 05, 2023
What is Presentation Layer?
The Presentation Layer is concerned with the syntax and semantics of the information exchanged between two communicating devices.
- The presentation layer takes care that the data is sent in that way the receiver of the data will understand the information (data) and will be able to use the data.
- Languages that are syntax can be different from the two communicating machines. In this condition, the presentation layer plays the role of translator between them.
- It is possible for two machines to communicate with different data representations, data structures to be exchanged can be defined in an abstract way.
- These abstract data structures will be managed by the presentation layer and this layer allows higher-level data structures (For example banking records), to be defined and exchanged.
This figure shows the relationship of the presentation layer to the session layer and application layer.

Design Issues with Presentation Layer
The following are the design issues with presentation layer:
- To manage and maintain the Syntax and Semantics of the information transmitted.
- Encoding data in a standard agreed-upon way just like a string, double, date, etc.
- It Performs Standard Encoding scheme on the wire.
Functionalities of the Presentation Layer
Specific functionalities of the presentation layer are as follows:
1. Translation
- The processes or running programs in two machines are usually exchanging the information in the form of numbers, character strings and so on before being transmitted. The information should be changed to bitstreams because different computers use different encoding schemes.
- The Presentation layer is responsible for compatibility between these encoding methods.
- The Presentation layer at the sender's side changes the information from its sender dependent format.
- The Presentation layer at the receiving machine changes the common format into its receivers dependent format.
Example: Convert ASCII code to EBCDIC code.
2. Encryption
- The system must be able to assure privacy regarding the message or information as it also carries sensitive information.
- Encryption means that the sender transforms the original information or message to another form, this data after encryption is known as the ciphertext and this ciphertext sends the resulting message out over the network.
- Decryption concerned with the transform of the message back to its original form. This decrypted data is known as plain text.
3. Compression
- Data Compression means reduces the number of bits to be transmitted by this reduce the bandwidth of the data.
- Data Compression becomes particularly important in the transmission of multimedia such as audio, video, text, etc.
Related Tutorials
- IPV4 Addressing | Classful and Classless Addressing
- Subnetting and Supernetting in Computer Network
- Network Address Translation (NAT) in Computer Network
- Fixed Length and Variable Length Subnet Mask (FLSM & VLSM)
- Line Configuration in Computer Network
- Transmission Modes in Computer Network
- Data Link Layer: What It Is, Sublayers, Design Issues, Functions
- Physical Layer: What It Is, Design Issues, Functions
- Network Layer: What It Is, Design Issues, Responsibilities
- Session Layer: What It Is, Design Issues, Functionalities
- Transport Layer: What It Is, Design Issues, Functions, and Example
- Optical Fiber (Fiber Optics) in Computer Network
- Unguided Transmission Media in Computer Network
- Virtual LAN (VLAN) in Computer Network
- Virtual Storage Area Networking (VSAN)
Comments and Discussions!
Load comments ↻
- Marketing MCQs
- Blockchain MCQs
- Artificial Intelligence MCQs
- Data Analytics & Visualization MCQs
- Python MCQs
- C++ Programs
- Python Programs
- Java Programs
- D.S. Programs
- Golang Programs
- C# Programs
- JavaScript Examples
- jQuery Examples
- CSS Examples
- C++ Tutorial
- Python Tutorial
- ML/AI Tutorial
- MIS Tutorial
- Software Engineering Tutorial
- Scala Tutorial
- Privacy policy
- Certificates
- Content Writers of the Month
Copyright © 2024 www.includehelp.com. All rights reserved.

Computer Network
- Operating Systems
- Computer Fundamentals
- Interview Q
Physical Layer
Data link layer, network layer, routing algorithm, transport layer, application layer, application protocols, network security.
Interview Questions
- Send your Feedback to [email protected]
Help Others, Please Share

Learn Latest Tutorials
Transact-SQL
Reinforcement Learning
R Programming
React Native
Python Design Patterns
Python Pillow
Python Turtle
Preparation

Verbal Ability

Company Questions
Trending Technologies
Artificial Intelligence
Cloud Computing
Data Science
Machine Learning
B.Tech / MCA
Data Structures
Operating System
Compiler Design
Computer Organization
Discrete Mathematics
Ethical Hacking
Computer Graphics
Software Engineering
Web Technology
Cyber Security
C Programming
Control System
Data Mining
Data Warehouse


IMAGES
VIDEO
COMMENTS
Prerequisite : OSI Model. Introduction : Presentation Layer is the 6th layer in the Open System Interconnection (OSI) model. This layer is also known as Translation layer, as this layer serves as a data translator for the network. The data which this layer receives from the Application Layer is extracted and manipulated here as per the required ...
The presentation layer is the lowest layer at which application programmers consider data structure and presentation, instead of simply sending data in the form of datagrams or packets between hosts. This layer deals with issues of string representation - whether they use the Pascal method (an integer length field followed by the specified ...
Chloe Tucker. This article explains the Open Systems Interconnection (OSI) model and the 7 layers of networking, in plain English. The OSI model is a conceptual framework that is used to describe how a network functions. In plain English, the OSI model helped standardize the way computer systems send information to each other.
The sixth layer of the OSI model is the Presentation layer. Applications running on the local system may or may not understand the format that is used to transmit the data over the network. The presentation layer works as a translator. When receiving data from the Application layer, it converts that data in such a format that can be sent over ...
In the seven-layer OSI model of computer networking, the presentation layer is layer 6 and serves as the data translator for the network. It is sometimes called the syntax layer. Description. Within the service layering semantics of the OSI network architecture, the presentation layer responds to service requests from the application layer and ...
7 Layers of the OSI Model. We will go through the different layers in detail below, but keep in mind that the upper layers (first 4) are about transport issues like the physical characteristics of the network and data transmission. The lower layers (last 3) are about application issues like data formatting and user interfacing.
In 1984, the open systems interconnection (OSI) model was published as a framework for network communication. The model breaks down computer network communication into seven layers. All of the layers work together to create a digital message. The message is built as it moves down the protocol stack. However, it is not sent to another network ...
The presentation layer is the 6 th layer from the bottom in the OSI model. This layer presents the incoming data from the application layer of the sender machine to the receiver machine. It converts one format of data to another format of data if both sender and receiver understand different formats; hence this layer is also called the ...
OSI model: Introduced as a comprehensive, protocol-independent framework, the OSI model details seven distinct layers, offering a more granular approach to network communication. TCP/IP model: Developed earlier by the U.S. Department of Defense, the TCP/IP model consists of four layers (Application, Transport, Internet and Network Access ...
The Presentation Layer is a crucial component of the OSI model, responsible for ensuring that data exchanged between systems is in a format that can be understood and used. By performing functions such as data translation, formatting, compression, and encryption, the Presentation Layer plays a vital role in maintaining data integrity ...
The presentation layer is located at Layer 6 of the OSI model. The tool that manages Hypertext Transfer Protocol ( HTTP) is an example of a program that loosely adheres to the presentation layer of OSI. Although it's technically considered an application-layer protocol per the TCP/IP model, HTTP includes presentation layer services within it.
The Open Systems Interconnection (OSI) model defines a networking framework to implement protocols in layers, with control passed from one layer to the next. It is primarily used today as a teaching tool. It conceptually divides computer network architecture into 7 layers in a logical progression. The lower layers deal with electrical signals ...
The presentation layer in the OSI model has five main functions within the frame of presentation layer protocols. Character Code Translation A character code is a representation of text using a ...
The Open Systems Interconnection (OSI) model is a reference model from the International Organization for Standardization (ISO) that "provides a common basis for the coordination of standards development for the purpose of systems interconnection." In the OSI reference model, the communications between systems are split into seven different abstraction layers: Physical, Data Link, Network ...
The Open Systems Interconnection model (OSI model) is a seven layer conceptual model that characterizes and standardizes the communication functions of a telecommunication or computing system. The physical layer, which is the bottom layer of the OSI model, is concerned with the transmission and reception of the unstructured raw bit stream over ...
The 7 layers of the OSI model. The layers are: Layer 1—Physical; Layer 2—Data Link; Layer 3—Network; Layer 4—Transport; Layer 5—Session; Layer 6—Presentation; Layer 7—Application. It ...
The seven Open Systems Interconnection layers are the following. Layer 7. The application layer. The application layer enables the user -- human or software -- to interact with the application or network whenever the user elects to read messages, transfer files or perform other network-related tasks.
Description and Functions of Presentation Layer in the OSI model: In this tutorial, we are going to learn what the Presentation layer is and the Functions of the Presentation Layer in the OSI model in Computer Networking. We will also discuss the Design issues with the Presentation Layer and the working of the Presentation Layer with the help of its diagram.
Each OSI model layer is part of a seven-stage stack. Information descends and ascends the stack as data flows through networks. In theory, the stacks represent critical processes in data transmission. These stages could include encryption, packet creation, flow management, and presentation.
Layer 3 - The Network Layer Layer 3, the network layer of the OSI model, provides an end-to-end logical addressing system so that a packet of data can be routed across several layer 2 networks (Ethernet,Token Ring, Frame Relay, etc.). Note that net-work layer addresses can also be referred to as logical addresses.
OSI Model. OSI stands for Open System Interconnection is a reference model that describes how information from a software application in one computer moves through a physical medium to the software application in another computer.; OSI consists of seven layers, and each layer performs a particular network function. OSI model was developed by the International Organization for Standardization ...
The presentation layer is the sixth layer of the Open Systems Interconnection (OSI), model. In computer networking, the OSI model is a concept that describes the transmission of data from one computer to another. Each layer in the model is a packet of protocols, or procedures that govern data transmission, which allow the layer to execute ...