- Skip to main content
- Skip to search
- Skip to footer

Products and Services

What is malware?
Malware, short for malicious software, refers to any intrusive software developed by cybercriminals (often called hackers) to steal data and damage or destroy computers and computer systems. Examples of common malware include viruses, worms, Trojan viruses, spyware, adware, and ransomware. Recent malware attacks have exfiltrated data in mass amounts.
What is the intent of malware?
Malware is developed as harmful software that invades or corrupts your computer network. The goal of malware is to cause havoc and steal information or resources for monetary gain or sheer sabotage intent.
Intelligence and intrusion
Exfiltrates data such as emails, plans, and especially sensitive information like passwords.
Disruption and extortion
Locks up networks and PCs, making them unusable. If it holds your computer hostage for financial gain, it's called ransomware.
Destruction or vandalism
Destroys computer systems to damage your network infrastructure.
Steal computer resources
Uses your computing power to run botnets, cryptomining programs (cryptojacking), or send spam emails.
Monetary gain
Sells your organization's intellectual property on the dark web.
How do I protect my network against malware?
Typically, businesses focus on preventative tools to stop breaches. By securing the perimeter, businesses assume they are safe. However, some advanced malware will eventually make their way into your network. As a result, it is crucial to deploy technologies that continually monitor and detect malware that has evaded perimeter defenses. Sufficient advanced malware protection requires multiple layers of safeguards along with high-level network visibility and intelligence.
Cisco Umbrella
Effectively protect your users against malware in minutes with fast, flexible, cloud-delivered security.
Secure Email
Rapidly detect, quarantine, investigate, and remediate cyberattacks that target your email.
Secure Firewall
Improve security with intelligent control points, unified, dynamic policies, and threat visibility.
How do I detect and respond to malware?
Malware will inevitably penetrate your network. You must have defenses that provide significant visibility and breach detection. To remove malware, you must be able to identify malicious actors quickly. This requires constant network scanning. Once the threat is identified, you must remove the malware from your network. Today's antivirus products are not enough to protect against advanced cyberthreats.
Learn how to update your antivirus strategy
Inside Cisco Talos Threat Hunters
Discover how Cisco Talos threat hunters identify new and evolving threats in the wild, and how their research and intelligence helps organizations build strong defenses.
7 types of malware
Viruses are a subgroup of malware. A virus is malicious software attached to a document or file that supports macros to execute its code and spread from host to host. Once downloaded, the virus will lie dormant until the file is opened and in use. Viruses are designed to disrupt a system's ability to operate. As a result, viruses can cause significant operational issues and data loss.
A worm is a type of malicious software that rapidly replicates and spreads to any device within the network. Unlike viruses, worms do not need host programs to disseminate. A worm infects a device through a downloaded file or a network connection before it multiplies and disperses at an exponential rate. Like viruses, worms can severely disrupt the operations of a device and cause data loss.
Trojan virus
Trojan viruses are disguised as helpful software programs. But once the user downloads it, the Trojan virus can gain access to sensitive data and then modify, block, or delete the data. This can be extremely harmful to the performance of the device. Unlike normal viruses and worms, Trojan viruses are not designed to self-replicate.
Spyware is malicious software that runs secretly on a computer and reports back to a remote user. Rather than simply disrupting a device's operations, spyware targets sensitive information and can grant remote access to predators. Spyware is often used to steal financial or personal information. A specific type of spyware is a keylogger, which records your keystrokes to reveal passwords and personal information.
Adware is malicious software used to collect data on your computer usage and provide appropriate advertisements to you. While adware is not always dangerous, in some cases adware can cause issues for your system. Adware can redirect your browser to unsafe sites, and it can even contain Trojan horses and spyware. Additionally, significant levels of adware can slow down your system noticeably. Because not all adware is malicious, it is important to have protection that constantly and intelligently scans these programs.
Ransomware is malicious software that gains access to sensitive information within a system, encrypts that information so that the user cannot access it, and then demands a financial payout for the data to be released. Ransomware is commonly part of a phishing scam. By clicking a disguised link, the user downloads the ransomware. The attacker proceeds to encrypt specific information that can only be opened by a mathematical key they know. When the attacker receives payment, the data is unlocked.
Fileless malware
Fileless malware is a type of memory-resident malware. As the term suggests, it is malware that operates from a victim's computer's memory, not from files on the hard drive. Because there are no files to scan, it is harder to detect than traditional malware. It also makes forensics more difficult because the malware disappears when the victim computer is rebooted. In late 2017, the Cisco Talos threat intelligence team posted an example of fileless malware that they called DNSMessenger.
What are the benefits of advanced malware protection?
Advanced malware can take the form of common malware that has been modified to increase its capability to infect. It can also test for conditions of a sandbox meant to block malicious files and attempt to fool security software into signaling that it is not malware. Advanced malware protection software is designed to prevent, detect, and help remove threats in an efficient manner from computer system.
Types of advanced malware protection
Related security topics
Malware protection best practices.
Explore how these 10 best practices can protect your business against malware attacks.
What is a firewall?
A firewall decides whether to allow or block specific traffic based on security rules.
What is phishing?
Phishing attacks are the practice of sending fraudulent communications that appear to come from a reputable source.
What is cybersecurity?
Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks.
What is network security?
Network security is the protection of the underlying networking infrastructure from unauthorized access, misuse, or theft.
What is ransomware?
Ransomware is a type of malicious software or malware. It encrypts a victim's data, after which the attacker demands a ransom.
Security Outcomes Report, Volume 3: Achieving Security Resilience
We asked 4700 security professionals from 26 countries to share success factors to boost security resilience.
- Home Products
- Small Business 1-49 employees
- Medium Business 50-999 employees
- Enterprise 1000+ employees
What are the different types of malware?

What does malware mean?
The word ‘malware’ is a contraction of ‘malicious software’. Malware is intrusive software that is intentionally designed to cause damage to computers and computer systems. By contrast, software that causes unintentional damage is usually referred to as a software bug.
People sometimes ask about the difference between a virus and malware. The difference is that malware is an umbrella term for a range of online threats, including viruses, spyware, adware, ransomware, and other types of harmful software. A computer virus is simply one type of malware.
Malware may be introduced to a network through phishing, malicious attachments, malicious downloads, social engineering , or flash drives. In this overview, we look at common malware types.
Types of malware
It’s important to understand the different types of malware attacks to help protect yourself from being compromised. While some malware categories are well-known (at least by name), others are less so:
Adware , a contraction of ‘advertising-supported software’, displays unwanted and sometimes malicious advertising on a computer screen or mobile device, redirects search results to advertising websites, and captures user data that can be sold to advertisers without the user's consent. Not all adware is malware, some is legitimate and safe to use.
Users can often affect the frequency of adware or what kinds of downloads they allow by managing the pop-up controls and preferences within their internet browsers or using an ad blocker.
Adware examples:
- Fireball – Fireball hit the headlines in 2017 when an Israeli software company discovered that 250 million computers and one-fifth of the corporate networks worldwide were infected with it. When Fireball affects your computer, it takes over your browser. It changes your homepage to a fake search engine – Trotus – and inserts obtrusive ads into any webpage you visit. It also prevents you from modifying your browser settings.
- Appearch – Appearch is another common adware program that acts as a browser hijacker. Usually bundled with other free software, it inserts so many ads into the browser that web browsing becomes very difficult. When you attempt to visit a website, you're taken to Appearch.info instead. If you manage to open a web page, Appearch converts random blocks of text into links, so when you select the text, a pop-up invites you to download software updates.
Spyware is a form of malware that hides on your device, monitors activity, and steals sensitive information like financial data, account information, logins, and more. Spyware can spread by exploiting software vulnerabilities or else be bundled with legitimate software or in Trojans.
Spyware examples:
- CoolWebSearch – This program took advantage of the security vulnerabilities in Internet Explorer to hijack the browser, change the settings, and send browsing data to its author.
- Gator – Usually bundled with file-sharing software like Kazaa, this program monitors the victim’s web surfing habits and uses the information to serve them with specific ads.
Ransomware and crypto-malware
Ransomware is malware designed to lock users out of their system or deny access to data until a ransom is paid. Crypto-malware is a type of ransomware that encrypts user files and requires payment by a specific deadline and often through a digital currency such as Bitcoin . Ransomware has been a persistent threat for organizations across industries for many years now. As more businesses embrace digital transformation, the likelihood of being targeted in a ransomware attack has grown considerably.
Ransomware examples:
- CryptoLocker is a form of malware prevalent in 2013 and 2014 which cyber criminals used to gain access to and encrypt files on a system. Cybercriminals used social engineering tactics to trick employees into downloading the ransomware onto their computers, infecting the network. Once downloaded, CryptoLocker would display a ransom message offering to decrypt the data if a cash or Bitcoin payment was made by the stated deadline. While the CryptoLocker ransomware has since been taken down, it is believed that its operators extorted around three million dollars from unsuspecting organizations.
- Phobos malware – a form of ransomware that appeared in 2019. This strain of ransomware is based on the previously known Dharma (aka CrySis) family of ransomware.
A Trojan (or Trojan Horse) disguises itself as legitimate software to trick you into executing malicious software on your computer. Because it looks trustworthy, users download it, inadvertently allowing malware onto their device. Trojans themselves are a doorway. Unlike a worm, they need a host to work. Once a Trojan is installed on a device, hackers can use it to delete, modify or capture data, harvest your device as part of a botnet, spy on your device, or gain access to your network.
Trojan examples:
- Qbot malware , also known as 'Qakbot' or 'Pinkslipbot', is a banking Trojan active since 2007 focused on stealing user data and banking credentials. The malware has evolved to include new delivery mechanisms, command and control techniques, and anti-analysis features.
- TrickBot malware —first identified in 2016—is a Trojan developed and operated by sophisticated cybercrime actors. Originally designed as a banking Trojan to steal financial data, TrickBot has evolved into modular, multi-stage malware that provides its operators with a full suite of tools to carry out numerous illegal cyber activities.
One of the most common types of malware, worms, spread over computer networks by exploiting operating system vulnerabilities. A worm is a standalone program that replicates itself to infect other computers without requiring action from anyone. Since they can spread fast, worms are often used to execute a payload—a piece of code created to damage a system. Payloads can delete files on a host system, encrypt data for a ransomware attack, steal information, delete files, and create botnets.
Worm example:
- SQL Slammer was a well-known computer worm that did not use traditional distribution methods. Instead, it generated random IP addresses and sent itself out to them, looking for those not protected by antivirus software. Soon after it hit in 2003, the result was more than 75,000 infected computers unknowingly involved in DDoS attacks on several major websites. Though the relevant security patch has been available for many years now, SQL Slammer nevertheless experienced a resurgence in 2016 and 2017.
A virus is a piece of code that inserts itself into an application and executes when the app is run. Once inside a network, a virus may be used to steal sensitive data, launch DDoS attacks, or conduct ransomware attacks. Usually spread via infected websites, file sharing, or email attachment downloads, a virus will lie dormant until the infected host file or program is activated. Once that happens, the virus can replicate itself and spread through your systems.
Virus example:
- Stuxnet – Stuxnet appeared in 2010 and was widely believed to have been developed by the US and Israeli governments to disrupt Iran’s nuclear program. Spread via a USB thumb drive, it targeted Siemens industrial control systems, causing centrifuges to fail and self-destroy at a record rate. It’s believed that Stuxnet infected over 20,000 computers and ruined one-fifth of Iran's nuclear centrifuges – setting its program back years.

A keylogger is a type of spyware that monitors user activity. Keyloggers can be used for legitimate purposes – for example, families who use them to keep track of their children's online activity or organizations which use them to monitor employee activity. However, when installed for malicious purposes, keyloggers can be used to steal password data, banking information, and other sensitive information. Keyloggers can be inserted into a system through phishing, social engineering, or malicious downloads.
Keylogger example:
- In 2017, a University of Iowa student was arrested after installing keyloggers on staff computers to steal login credentials to modify and change grades. The student was found guilty and sentenced to four months in prison .
Bots and botnets
A bot is a computer that has been infected with malware so it can be controlled remotely by a hacker. The bot – sometimes called a zombie computer – can then be used to launch more attacks or become part of a collection of bots called a botnet . Botnets can include millions of devices as they spread undetected. Botnets help hackers with numerous malicious activities, including DDoS attacks, sending spam and phishing messages , and spreading other types of malware.
Botnet examples:
- Andromeda malware – The Andromeda botnet was associated with 80 different malware families. It grew so large that it was at one point infecting a million new machines a month, distributing itself via social media, instant messaging, spam emails, exploit kits, and more. The operation was taken down by the FBI, Europol's European Cybercrime centre, and others in 2017 – but many PCs continued to be infected.
- Mirai – In 2016, a massive DDoS attack left much of the US East Coast without internet access. The attack, which authorities initially feared was the work of a hostile nation-state, was caused by the Mirai botnet. Mirai is a type of malware that automatically finds Internet of Things (IoT) devices to infect and conscripts them into a botnet. From there, this IoT army can be used to mount DDoS attacks in which a firehose of junk traffic floods a target's servers with malicious traffic. Mirai continues to cause trouble today .
PUP malware
PUPs – which stands for ‘potentially unwanted programs’ – are programs that may include advertising, toolbars, and pop-ups that are unrelated to the software you downloaded. Strictly speaking, PUPs are not always malware – PUP developers point out that their programs are downloaded with their users’ consent, unlike malware. But it is widely recognized that people mainly download PUPs because they have failed to realize that they have agreed to do so.
PUPs are often bundled with other more legitimate pieces of software. Most people end up with a PUP because they have downloaded a new program and didn’t read the small print when installing it – and therefore didn’t realize they were opting in for additional programs that serve no real purpose.
PUP malware example:
- Mindspark malware – this was an easily installable PUP which ended up on users’ machines without them noticing the download. Mindspark can change settings and trigger behavior on the device without the user’s knowledge. It is notoriously difficult to eliminate.
Today, most malware is a combination of different types of malicious software, often including parts of Trojans and worms and occasionally a virus. Usually, the malware program appears to the end-user as a Trojan, but once executed, it attacks other victims over the network like a worm.
Hybrid malware example:
- In 2001, a malware developer calling himself ‘Lion’ released a hybrid malware — a worm/rootkit combination. Rootkits allow hackers to manipulate operating system files, while worms are powerful vectors for rapidly spreading code pieces. This malicious combination caused havoc: it inflicted damage on more than 10,000 Linux systems. Worm/rootkit combination malware was explicitly designed to exploit the vulnerabilities in Linux systems.
Fileless malware
Fileless malware is a type of malicious software that uses legitimate programs to infect a computer. It does not rely on files and leaves no footprint, making it challenging to detect and remove. Fileless malware emerged in 2017 as a mainstream type of attack, but many of these attack methods have been around for a while.
Without being stored in a file or installed directly on a machine, fileless infections go straight into memory, and the malicious content never touches the hard drive. Cybercriminals have increasingly turned to fileless malware as an effective alternative form of attack, making it more difficult for traditional antivirus to detect because of the low footprint and the absence of files to scan.
Fileless malware examples:
- Frodo, Number of the Beast, and The Dark Avenger were all early examples of this type of malware.
Logic bombs
Logic bombs are a type of malware that will only activate when triggered, such as on a specific date and time or on the 20th log-on to an account. Viruses and worms often contain logic bombs to deliver their payload (i.e., malicious code) at a pre-defined time or when another condition is met. The damage caused by logic bombs varies from changing bytes of data to making hard drives unreadable.
Logic bomb example:
- In 2016, a programmer caused spreadsheets to malfunction at a branch of the Siemens corporation every few years, so that they had to keep hiring him back to fix the problem. In this case, nobody suspected anything until a coincidence forced the malicious code out into the open.
How does malware spread?
The most common ways in which malware threats can spread include:
- Email: If your email has been hacked, malware can force your computer to send emails with infected attachments or links to malicious websites. When a recipient opens the attachment or clicks the link, the malware is installed on their computer, and the cycle repeats.
- Physical media: Hackers can load malware onto USB flash drives and wait for unsuspecting victims to plug them into their computers. This technique is often used in corporate espionage.
- Pop-up alerts: This includes fake security alerts which trick you into downloading bogus security software, which in some cases can be additional malware.
- Vulnerabilities: A security defect in software can allow malware to gain unauthorized access to the computer, hardware, or network.
- Backdoors: An intended or unintended opening in software, hardware, networks, or system security.
- Drive-by downloads: Unintended download of software with or without knowledge of the end-user.
- Privilege escalation: A situation where an attacker obtains escalated access to a computer or network and then uses it to launch an attack.
- Homogeneity: If all systems are running the same operating system and connected to the same network, the risk of a successful worm spreading to other computers is increased.
- Blended threats: Malware packages that combine characteristics from multiple types of malware, making them harder to detect and stop because they can exploit different vulnerabilities.
Signs of a malware infection
If you’ve noticed any of the following, you may have malware on your device:
- A slow, crashing, or freezing computer
- The infamous ‘blue screen of death’
- Programs opening and closing automatically or altering themselves
- Lack of storage space
- Increased pop-ups, toolbars, and other unwanted programs
- Emails and messages being sent without you initiating them
Use antivirus to protect you from malware threats:
The best way to protect yourself from a malware attack and potentially unwanted programs is through using a comprehensive antivirus. Kaspersky Total Security provides 24/7 protection against hackers, viruses, and malware – helping to keep your data and devices secure.
Related articles:
- Who creates malware?
- What’s the difference between a virus and a worm?
- How do computer viruses work?
- Top ransomware of 2020
Featured Articles

Black Friday Scams: How to Shop Safely Online

What is a dark web scan?

The Biggest Crypto Exchange Hacks: How to Make Sure You Protect Your Crypto Against Hacks

What Can Hackers Do With Your Email Address?

What is SIM Swapping?
We use cookies to make your experience of our websites better. By using and further navigating this website you accept this. Detailed information about the use of cookies on this website is available by clicking on more information .

- My presentations
Auth with social network:
Download presentation
We think you have liked this presentation. If you wish to download it, please recommend it to your friends in any social system. Share buttons are a little bit lower. Thank you!
Presentation is loading. Please wait.
Introduction to MALWARE
Published by Silas Hopkins Modified over 6 years ago
Similar presentations
Presentation on theme: "Introduction to MALWARE"— Presentation transcript:
Providing protection from potential security threats that exist for any internet-connected computer is termed e- security. It is important to be able to.
Thank you to IT Training at Indiana University Computer Malware.
Protect your PC virus, worm, Trojan horse, phishing, spam, botnet and zombies, spoofing, social engineering, identity theft, spyware, rootkits Click.
Dr. John P. Abraham Professor UTPA 2 – Systems Threats and Risks.
Telnet and FTP. Telnet Lets you use the resources of some other computer on the Internet to access files, run programs, etc. Creates interactive connection.
Downloading + Viruses. Downloading Modems (56K) V.90 DSL (digital subscriber line) Cable Modem Satellite.
Threats To A Computer Network
Chapter 14 Computer Security Threats Patricia Roy Manatee Community College, Venice, FL ©2008, Prentice Hall Operating Systems: Internals and Design Principles,
Henric Johnson1 Chapter 10 Malicious Software Henric Johnson Blekinge Institute of Technology, Sweden
Securing Windows 7 Lesson 10. Objectives Understand authentication and authorization Configure password policies Secure Windows 7 using the Action Center.
Computer Security: Principles and Practice First Edition by William Stallings and Lawrie Brown Lecture slides by Lawrie Brown Chapter 7 – Malicious Software.
Malicious Software Malicious Software Han Zhang & Ruochen Sun.
1 Ola Flygt Växjö University, Sweden Malicious Software.
1 Chap 10 Malicious Software. 2 Viruses and ”Malicious Programs ” Computer “Viruses” and related programs have the ability to replicate themselves on.
© 2007 Cisco Systems, Inc. All rights reserved.Cisco Public ITE PC v4.0 Chapter 1 1 Basic Security Networking for Home and Small Businesses – Chapter 8.
Network and Internet Security SYSTEM SECURITY. Virus Countermeasures Antivirus approach ◦Ideal solution: Prevention ◦Not allowing the virus to infect.
Detrick Robinson & Amris Treadwell. Computer viruses- are pieces of programs that are purposely made up to infect your computer. Examples: › Internet.
Hacker Zombie Computer Reflectors Target.
ITIS 1210 Introduction to Web-Based Information Systems Chapter 45 How Hackers can Cripple the Internet and Attack Your PC How Hackers can Cripple the.
Lecture 14 Overview. Program Flaws Taxonomy of flaws: – how (genesis) – when (time) – where (location) the flaw was introduced into the system 2 CS 450/650.
About project
© 2024 SlidePlayer.com Inc. All rights reserved.
Got any suggestions?
We want to hear from you! Send us a message and help improve Slidesgo
Top searches
Trending searches

holy spirit
35 templates

11 templates

business pitch
598 templates

ai technology
169 templates
21 templates
environmental science
36 templates
Malware Infographics
It seems that you like this template, free google slides theme, powerpoint template, and canva presentation template.
Cybersecurity is a must in most companies nowadays. Keep your employees up to date with the world of malware by editing and inserting these infographics into your presentations. You can provide data and statistics about different antivirus software and how to prevent hacking, phishing and other things. Our designs come in various forms: banners, pie charts, bar graphs... Choose your preferred one and start working on it!
Features of these infographics
- 100% editable and easy to modify
- 31 different infographics to boost your presentations
- Include icons and Flaticon’s extension for further customization
- Designed to be used in Google Slides, Canva, and Microsoft PowerPoint and Keynote
- 16:9 widescreen format suitable for all types of screens
- Include information about how to edit and customize your infographics
How can I use the infographics?
Am I free to use the templates?
How to attribute the infographics?
Attribution required If you are a free user, you must attribute Slidesgo by keeping the slide where the credits appear. How to attribute?
Related posts on our blog.

How to Add, Duplicate, Move, Delete or Hide Slides in Google Slides

How to Change Layouts in PowerPoint
How to Change the Slide Size in Google Slides
Related presentations.
Premium template
Unlock this template and gain unlimited access
- Engineering Mathematics
- Discrete Mathematics
- Operating System
- Computer Networks
- Digital Logic and Design
- C Programming
- Data Structures
- Theory of Computation
- Compiler Design
- Computer Org and Architecture
- Cyber Security Tutorial
Introduction
- OSI Security Architecture
- Active and Passive attacks in Information Security
- Types of Security Mechanism
- A Model for Network Security

Cyber Technology
- Basics of Wi-Fi
- The Internet and the Web
- What is a Website ?
- Cryptography and Network Security Principles
- Public Key Infrastructure
- What is Electronic Signature?
- Identity and Access Management
- What Is Cloud Computing ?
Cyber Ethics
- Intellectual Property Rights
- Fundamental Rights (Articles 12-35): A Comprehensive Guide
- Introduction to Ethical Hacking
- What is a Scam?
Cyber Crimes
- Psychological Profiling in Cybersecurity
- Social Engineering - The Art of Virtual Exploitation
- Cyber Stalking
- How to Defend Against Botnets ?
- Emerging Attack Vectors in Cyber Security
Malware and its types
- What is Phishing?
- Cyber Crime - Identity Theft
- What is Cyber Terrorism?
- What is Proxy Server?
Cyber Crime Techniques
- Worms, Viruses and beyond !!
- Trojan Horse in Information Security
Keyloggers and Spyware
- Types of SQL Injection (SQLi)
- Buffer Overflow Attack with Example
- Reverse Engineering - Software Engineering
- Difference Between Vulnerability and Exploit
- Basic Network Attacks in Computer Network
- Kali Linux - Hacking Wi-Fi
- Web Server and its Types of Attacks
- Types of VoIP Hacking and Countermeasures
- How to Spoof SMS Message in Linux ?
- Difference between Backup and Recovery
- Manual Code Review : Security Assessment
- Penetration Testing - Software Engineering
Prevention and Protection
- What is Vulnerability Assessment?
- Secure coding - What is it all about?
- Chain of Custody - Digital Forensics
- Digital Forensics in Information Security
- Introduction of Computer Forensics
- What is Network Forensics?
Cyber Forensics
- Cybercrime Causes And Measures To Prevent It
- Digital Evidence Collection in Cybersecurity
- Digital Evidence Preservation - Digital Forensics
- Computer Forensic Report Format
- How to Stop Phishing?
Cyber Crime Investigation
- Intellectual Property in Cyberspace
- Cyber Security Policy
- History of Cyber Security
- What is Internet? Definition, Uses, Working, Advantages and Disadvantages
- Cyber Security Metrics
- What is Cybersecurity Framework?
- Cyber Security, Types and Importance
Cyber security Evolution
- Substitution Cipher
- Difference between Substitution Cipher Technique and Transposition Cipher Technique
- Difference between Block Cipher and Transposition Cipher
Cyber security Objectives
- Data encryption standard (DES) | Set 1
- Strength of Data encryption standard (DES)
- Differential and Linear Cryptanalysis
Classical Encryption Techniques
- Difference between AES and DES ciphers
- Advanced Encryption Standard (AES)
Block Ciphers and the Data Encryption Standard
- Implementation of RC4 algorithm
- Introduction to Chinese Remainder Theorem
- Discrete logarithm (Find an integer k such that a^k is congruent modulo b)
- Public Key Encryption
Advanced Encryption Standard
- Key Management in Cryptography
- Implementation of Diffie-Hellman Algorithm
Moreon Symmetric Ciphers
- Message Authentication Requirements
- How message authentication code works?
- Hash Functions in System Security
Introduction to Number Theory
- Whirlpool Hash Function in Python
- HMAC Algorithm in Computer Network
Public-Key Cryptography and RSA
- Types of Authentication Protocols
- Digital Signature Standard (DSS)
Key Management:OtherPublic-Key Cryptosystems
- X.509 Authentication Service
- PGP - Authentication and Confidentiality
Message Authentication and Hash Functions
- IP security (IPSec)
- IPSec Architecture
- Internet Protocol Authentication Header
Hashand MAC Algorithms
- Web Security Considerations
- Secure Socket Layer (SSL)
- Transport Layer Security (TLS)
Digital Signatures and Authentication Protocols
- Intruders in Network Security
- Password Management in Cyber Security
Authentication Applications
Electronic mail security, ip security, web security, malicious software.
Any malicious software intended to harm or exploit any programmable device, service, or network is referred to as malware. Cybercriminals typically use it to extract data they can use against victims to their advantage in order to profit financially. Financial information, medical records, personal emails, and passwords are just a few examples of the types of information that could be compromised.
In simple words, malware is short for malicious software and refers to any software that is designed to cause harm to computer systems, networks, or users. Malware can take many forms. It’s important for individuals and organizations to be aware of the different types of malware and take steps to protect their systems, such as using antivirus software, keeping software and systems up-to-date, and being cautious when opening email attachments or downloading software from the internet.
Malware is a program designed to gain access to computer systems, generally for the benefit of some third party, without the user’s permission. Malware includes computer viruses , worms, Trojan horses, ransomware , spyware, and other malicious programs.
Why Do Cybercriminals Use Malware?
- Cybercriminals use malware, which includes all forms of malicious software including viruses, for a variety of purposes.
- Using deception to induce a victim to provide personal information for identity theft
- Theft of customer credit card information or other financial information
- Taking over several computers and using them to launch denial-of-service attacks against other networks
- Using infected computers to mine for cryptocurrencies like bitcoin .
Types of Malware
- Viruses – A Virus is a malicious executable code attached to another executable file. The virus spreads when an infected file is passed from system to system. Viruses can be harmless or they can modify or delete data. Opening a file can trigger a virus. Once a program virus is active, it will infect other programs on the computer.
- Worms – Worms replicate themselves on the system, attaching themselves to different files and looking for pathways between computers, such as computer network that shares common file storage areas. Worms usually slow down networks. A virus needs a host program to run but worms can run by themselves. After a worm affects a host, it is able to spread very quickly over the network.
- Trojan horse – A Trojan horse is malware that carries out malicious operations under the appearance of a desired operation such as playing an online game. A Trojan horse varies from a virus because the Trojan binds itself to non-executable files, such as image files, and audio files.
- Ransomware – Ransomware grasps a computer system or the data it contains until the victim makes a payment. Ransomware encrypts data in the computer with a key that is unknown to the user. The user has to pay a ransom (price) to the criminals to retrieve data. Once the amount is paid the victim can resume using his/her system
- Adware – It displays unwanted ads and pop-ups on the computer. It comes along with software downloads and packages. It generates revenue for the software distributer by displaying ads.
- Spyware – Its purpose is to steal private information from a computer system for a third party. Spyware collects information and sends it to the hacker.
- Logic Bombs – A logic bomb is a malicious program that uses a trigger to activate the malicious code. The logic bomb remains non-functioning until that trigger event happens. Once triggered, a logic bomb implements a malicious code that causes harm to a computer. Cybersecurity specialists recently discovered logic bombs that attack and destroy the hardware components in a workstation or server including the cooling fans, hard drives, and power supplies. The logic bomb overdrives these devices until they overheat or fail.
- Rootkits – A rootkit modifies the OS to make a backdoor. Attackers then use the backdoor to access the computer distantly. Most rootkits take advantage of software vulnerabilities to modify system files.
- Backdoors – A backdoor bypasses the usual authentication used to access a system. The purpose of the backdoor is to grant cyber criminals future access to the system even if the organization fixes the original vulnerability used to attack the system.
- Keyloggers – Keylogger records everything the user types on his/her computer system to obtain passwords and other sensitive information and send them to the source of the keylogging program.
How To Know If Our Devices Are Infected With Malware?
The following are the most typical indications that malware has compromised your computer:
- Performing poorly on the computer by execution.
- When your web browser directs you to a website you didn’t intend to visit, this is known as a browser redirect.
- Warnings about infections are frequently accompanied by offers to buy a product to treat them.
- Having trouble starting or shutting down your computer.
- Persistent pop-up ads.
How To Protect From Malware?
The good news is that there are just as many ways to protect yourself from malware as there are different types of malware. Look at these top suggestions:
- Protect your devices.
- Update your operating system and software. Install updates as soon as they become available because cybercriminals search for vulnerabilities in out-of-date or outdated software.
- Never click on a popup’s link. Simply click the “X” in the message’s upper corner to close it and leave the page that generated it.
- Don’t install too many apps on your devices. Install only the apps you believe you will regularly use and need.
- Be cautious when using the internet.
- Do not click on unidentified links. If a link seems suspicious, avoid clicking it whether it comes from an email, social networking site, or text message.
- Choose the websites you visit wisely. Use a safe search plug-in and try to stick to well-known and reputable websites to avoid any that might be malicious without your knowledge.
- Emails requesting personal information should be avoided. Do not click a link in an email that appears to be from your bank and asks you to do so in order to access your account or reset your password. Log in immediately at your online banking website.
How To Remove Malware?
As was already mentioned, a large number of security software programs are made to both find and stop malware as well as to eliminate it from infected systems.
An antimalware tool that handles malware detection and removal is Malwarebytes. Malware can be eliminated from Windows, macOS, Android, and iOS operating systems. A user’s registry files, currently running programs, hard drives, and individual files can all be scanned by Malwarebytes. Malware can then be quarantined and removed if it is found. Users cannot, however, set automatic scanning schedules like they can with some other tools.
Advantages of Detecting and Removing Malware
- Improved Security: By detecting and removing malware, individuals, and organizations can improve the security of their systems and reduce the risk of future infections.
- Prevent Data Loss: Malware can cause data loss, and by removing it, individuals and organizations can protect their important files and information.
- Protect Reputation: Malware can cause harm to a company’s reputation, and by detecting and removing it, individuals and organizations can protect their image and brand.
- Increased Productivity: Malware can slow down systems and make them less efficient, and by removing it, individuals and organizations can increase the productivity of their systems and employees.
Disadvantages of Detecting and Removing Malware
- Time-Consuming: The process of detecting and removing malware can be time-consuming and require specialized tools and expertise.
- Cost: Antivirus software and other tools required to detect and remove malware can be expensive for individuals and organizations.
- False Positives: Malware detection and removal tools can sometimes result in false positives, causing unnecessary alarm and inconvenience.
- Difficulty: Malware is constantly evolving, and the process of detecting and removing it can be challenging and require specialized knowledge and expertise.
- Risk of Data Loss: Some malware removal tools can cause unintended harm, resulting in data loss or system instability.
Please Login to comment...
Similar reads.
- Information-Security
Improve your Coding Skills with Practice
What kind of Experience do you want to share?
- Malware Attacks
- Popular Categories
Powerpoint Templates
Icon Bundle
Kpi Dashboard
Professional
Business Plans
Swot Analysis
Gantt Chart
Business Proposal
Marketing Plan
Project Management
Business Case
Business Model
Cyber Security
Business PPT
Digital Marketing
Digital Transformation
Human Resources
Product Management
Artificial Intelligence
Company Profile
Acknowledgement PPT
PPT Presentation
Reports Brochures
One Page Pitch
Interview PPT
All Categories
Powerpoint Templates and Google slides for Malware Attacks
Save your time and attract your audience with our fully editable ppt templates and slides..
Item 1 to 60 of 106 total items
- You're currently reading page 1

This complete presentation has PPT slides on wide range of topics highlighting the core areas of your business needs. It has professionally designed templates with relevant visuals and subject driven content. This presentation deck has total of sixty two slides. Get access to the customizable templates. Our designers have created editable templates for your convenience. You can edit the colour, text and font size as per your need. You can add or delete the content if required. You are just a click to away to have this ready made presentation. Click the download button now.

Presenting Malware Attack in Cyber Security. These slides are 100 percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.

Deliver a credible and compelling presentation by deploying this Malware Attack Powerpoint Ppt Template Bundles. Intensify your message with the right graphics, images, icons, etc. presented in this complete deck. This PPT template is a great starting point to convey your messages and build a good collaboration. The twenty slides added to this PowerPoint slideshow helps you present a thorough explanation of the topic. You can use it to study and present various kinds of information in the form of stats, figures, data charts, and many more. This Malware Attack Powerpoint Ppt Template Bundles PPT slideshow is available for use in standard and widescreen aspects ratios. So, you can use it as per your convenience. Apart from this, it can be downloaded in PNG, JPG, and PDF formats, all completely editable and modifiable. The most profound feature of this PPT design is that it is fully compatible with Google Slides making it suitable for every industry and business domain.
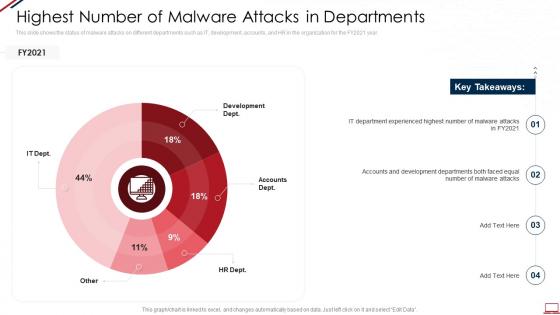
This slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2021 year. Present the topic in a bit more detail with this Computer System Security Highest Number Of Malware Attacks In Departments. Use it as a tool for discussion and navigation on Development Dept, Accounts Dept, HR Dept, Other, IT Dept. This template is free to edit as deemed fit for your organization. Therefore download it now.
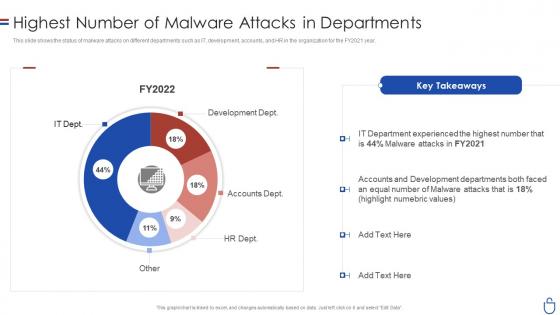
This slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2021 year. Deliver an outstanding presentation on the topic using this Data Security IT Highest Number Of Malware Attacks In Departments. Dispense information and present a thorough explanation of Development Dept, Accounts Dept, HR Dept using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
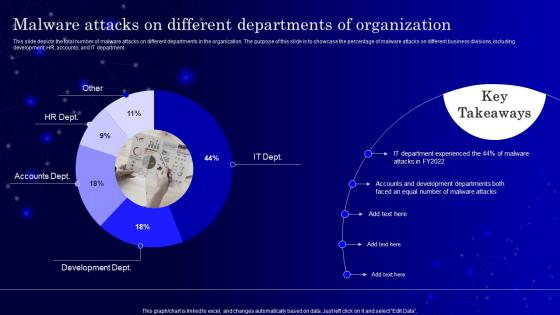
This slide depicts the total number of malware attacks on different departments in the organization. The purpose of this slide is to showcase the percentage of malware attacks on different business divisions, including development, HR, accounts, and IT department. Present the topic in a bit more detail with this Secops V2 Malware Attacks On Different Departments Of Organization. Use it as a tool for discussion and navigation on Malware Attacks, Development Departments, Accounts Departments. This template is free to edit as deemed fit for your organization. Therefore download it now.
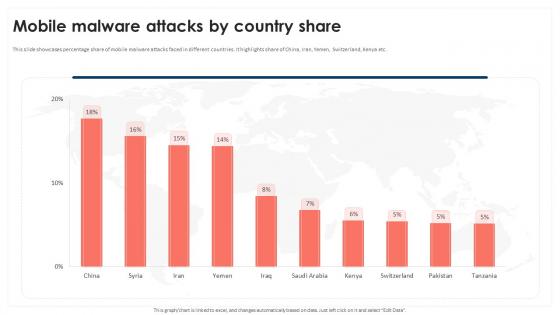
This slide showcases percentage share of mobile malware attacks faced in different countries. It highlights share of China, Iran, Yemen, Switzerland, Kenya etc. Present the topic in a bit more detail with this Mobile Malware Attacks By Country Share Mobile Device Security Cybersecurity SS Use it as a tool for discussion and navigation on Purpose, Scope, Loss And Theft This template is free to edit as deemed fit for your organization. Therefore download it now.
Presenting our set of slides with CTI Cybersecurity Icon To Prevent Malware Infections And Attacks This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on CTI Cybersecurity Icon, Prevent Malware Infections And Attacks
Introducing our premium set of slides with Cybersecurity Infrastructure Icon To Prevent Malware Attacks Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cybersecurity Infrastructure, Icon To Prevent, Malware Attacks So download instantly and tailor it with your information.
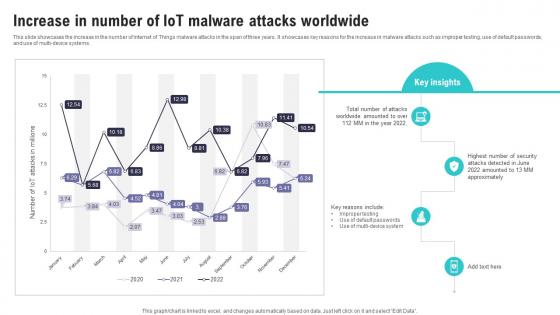
This slide showcases the increase in the number of Internet of Things malware attacks in the span of three years. It showcases key reasons for the increase in malware attacks such as improper testing, use of default passwords, and use of multi device systems. Present the topic in a bit more detail with this Increase In Number Of IoT Malware Attacks Worldwide IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Worldwide Amounted, Default Passwords, Attacks Detected. This template is free to edit as deemed fit for your organization. Therefore download it now.
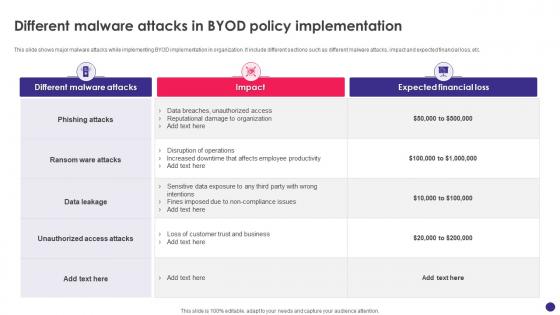
This slide shows major malware attacks while implementing BYOD implementation in organization. It include different sections such as different malware attacks, impact and expected financial loss, etc. Present the topic in a bit more detail with this Implementing Byod Policy To Enhance Different Malware Attacks In Byod Policy Implementation. Use it as a tool for discussion and navigation on Phishing Attacks, Ransom Ware Attacks, Data Leakage, Unauthorized Access Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
Presenting our set of slides with name Malware Threat Attack Icon For DOS Attack Prevention. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware Threat ,Attack Icon, DOS Attack Prevention.
Presenting our set of slides with name Server Malware Icon For Efficient DOS Attack. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Server Malware Icon, Efficient DOS Attack.
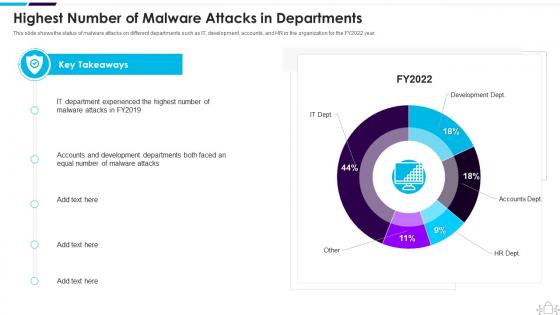
This slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2022 year. Present the topic in a bit more detail with this Information Technology Security Highest Number Of Malware Attacks In Departments. Use it as a tool for discussion and navigation on Department, Experienced, Malware. This template is free to edit as deemed fit for your organization. Therefore download it now.
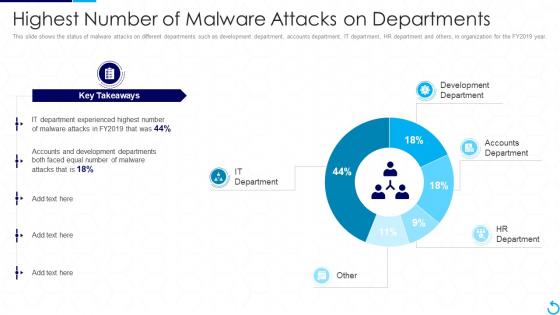
This slide shows the status of malware attacks on different departments such as development department, accounts department, IT department, HR department and others, in organization for the FY2019 year. Present the topic in a bit more detail with this Reverse Proxy It Highest Number Of Malware Attacks On Departments. Use it as a tool for discussion and navigation on Departments, Development, Experienced. This template is free to edit as deemed fit for your organization. Therefore download it now.
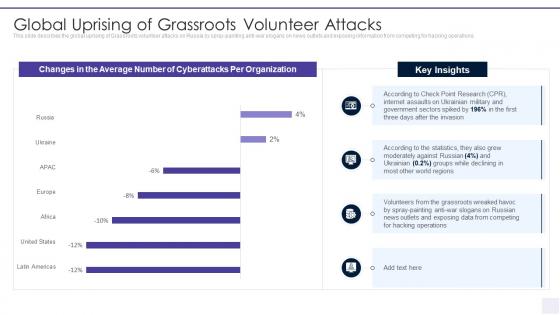
This slide describes the global uprising of Grassroots volunteer attacks on Russia by spray painting anti war slogans on news outlets and exposing information from competing for hacking operations. Present the topic in a bit more detail with this Wiper Malware Attack Global Uprising Of Grassroots Volunteer Attacks. Use it as a tool for discussion and navigation on Global Uprising Of Grassroots Volunteer Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
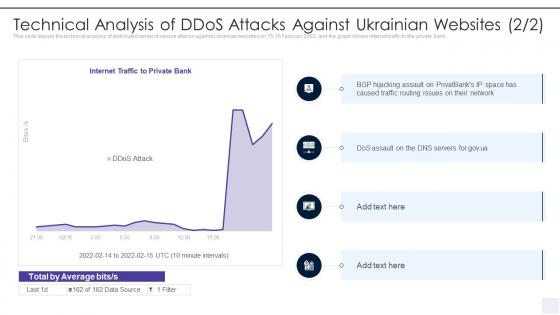
This slide depicts the technical analysis of distributed denial of service attacks against Ukrainian websites on 15 16 February 2022, and the graph shows internet traffic to the private bank. Deliver an outstanding presentation on the topic using this Wiper Malware Attack Technical Analysis Of DDOS Attacks Against. Dispense information and present a thorough explanation of Technical Analysis Of Ddos Attacks Against Ukrainian Websites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
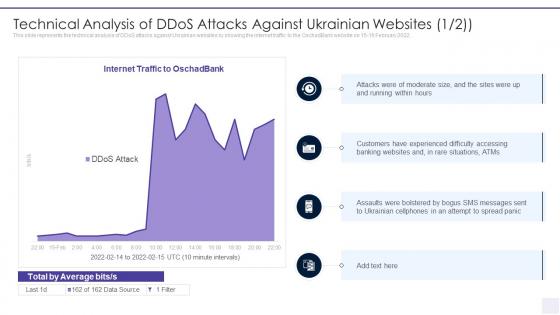
This slide represents the technical analysis of DDoS attacks against Ukrainian websites by showing the internet traffic to the OschadBank website on 15 16 February 2022. Present the topic in a bit more detail with this Technical Analysis Of Ddos Attacks Against Ukrainian Wiper Malware Attack. Use it as a tool for discussion and navigation on Technical Analysis Of Ddos Attacks Against Ukrainian Websites. This template is free to edit as deemed fit for your organization. Therefore download it now.
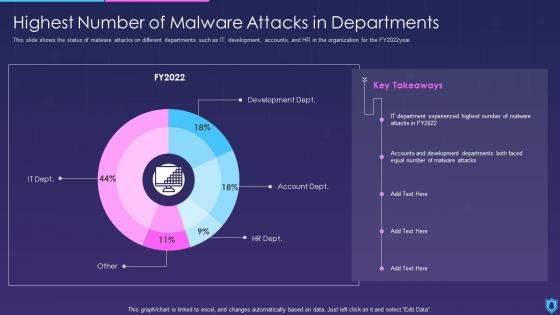
This slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2022year. Present the topic in a bit more detail with this Information Security Highest Number Of Malware Attacks In Departments. Use it as a tool for discussion and navigation on Departments, Malware, Development. This template is free to edit as deemed fit for your organization. Therefore download it now.
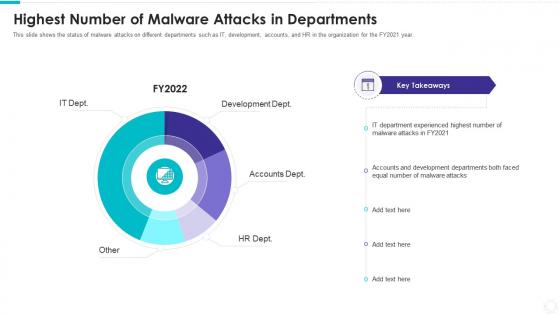
This slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2021 year. Present the topic in a bit more detail with this Electronic Information Security Highest Number Malware Attacks Departments. Use it as a tool for discussion and navigation on Development Dept, Accounts Dept, HR Dept, Other, IT Dept. This template is free to edit as deemed fit for your organization. Therefore download it now.
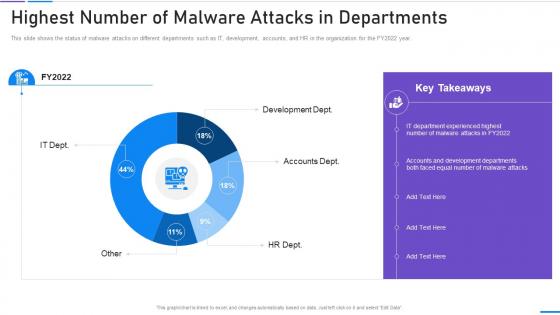
This slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2022 year. Present the topic in a bit more detail with this Network Security Highest Number Of Malware Attacks In Departments. Use it as a tool for discussion and navigation on Highest Number Of Malware Attacks In Departments. This template is free to edit as deemed fit for your organization. Therefore download it now.
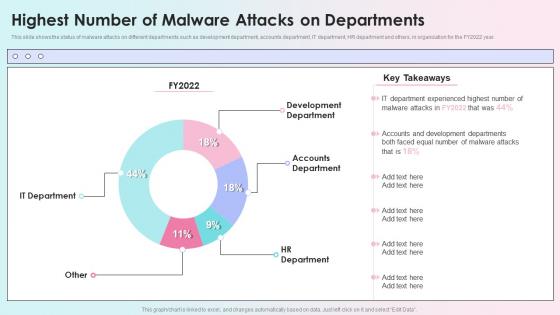
This slide shows the status of malware attacks on different departments such as development department, accounts department, IT department, HR department and others, in organization for the FY2022 year. Present the topic in a bit more detail with this Highest Number Of Malware Attacks On Departments Reverse Proxy Load Balancer Ppt Infographics. Use it as a tool for discussion and navigation on Development Department, Accounts Department, Hr Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
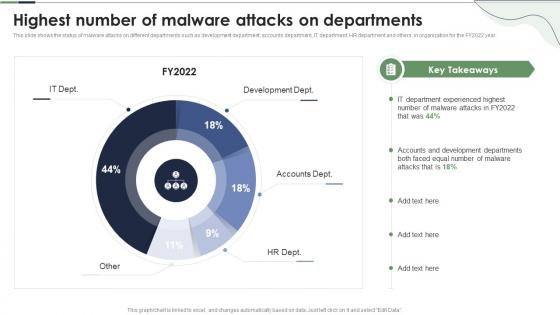
This slide shows the status of malware attacks on different departments such as development department, accounts department, IT department, HR department and others, in organization for the FY2022 year. Present the topic in a bit more detail with this Highest Number Of Malware Attacks On Departments Reverse Proxy Server Ppt Powerpoint Presentation Professional. Use it as a tool for discussion and navigation on Highest Number, Development Dept, Accounts Dept. This template is free to edit as deemed fit for your organization. Therefore download it now.
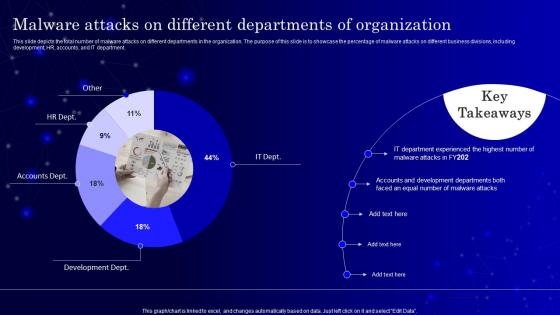
This slide depicts the total number of malware attacks on different departments in the organization. The purpose of this slide is to showcase the percentage of malware attacks on different business divisions, including development, HR, accounts, and IT department. Present the topic in a bit more detail with this SecOps Malware Attacks On Different Departments Of Organization Ppt Portrait. Use it as a tool for discussion and navigation on It Department, Accounts Development. This template is free to edit as deemed fit for your organization. Therefore download it now.

Following slides shows the various campaign plan organize in organization regarding cyber awareness to reduce the threat. It includes various campaign.Introducing our Malware Attack Awareness Training Program In Organization set of slides. The topics discussed in these slides are Highly Employee, Security Awareness, Least Affected. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
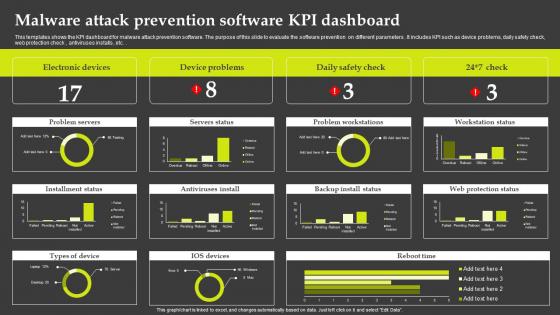
This templates shows the KPI dashboard for malware attack prevention software. The purpose of this slide to evaluate the software prevention on different parameters . It includes KPI such as device problems, daily safety check, web protection check , antiviruses installs , etc.Introducing our Malware Attack Prevention Software KPI Dashboard set of slides. The topics discussed in these slides are Electronic Devices, Device Problems, Problem Workstations. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
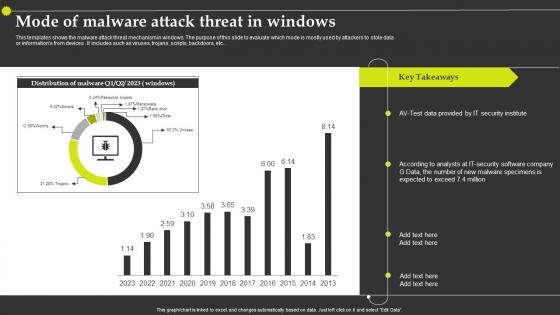
This templates shows the malware attack threat mechanism in windows. The purpose of this slide to evaluate which mode is mostly used by attackers to stole data or informations from devices . It includes such as viruses, trojans, scripts, backdoors, etc.Introducing our Mode Of Malware Attack Threat In Windows set of slides. The topics discussed in these slides are Security Institute, Malware Specimens, Security Software Company. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
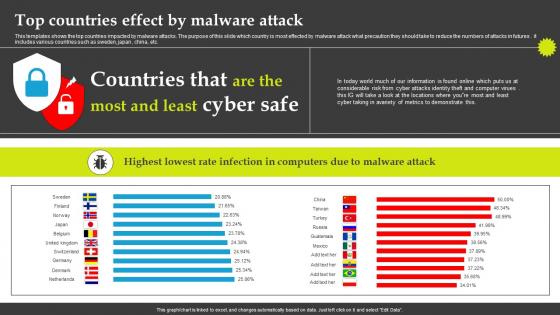
This templates shows the top countries impacted by malware attacks. The purpose of this slide which country is most effected by malware attack what precaution they should take to reduce the numbers of attacks in futures . it includes various countries such as sweden, japan , china, etc. Introducing our Top Countries Effect By Malware Attack set of slides. The topics discussed in these slides are Information Found, Metrics Demonstrate, Infection Computers. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
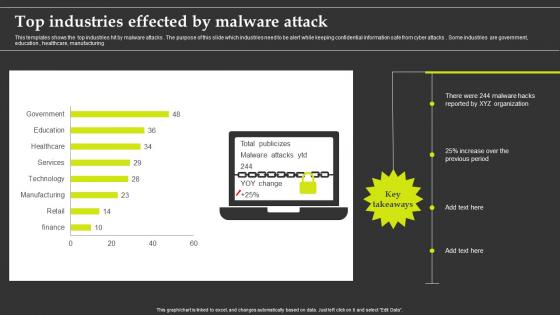
This templates shows the top industries hit by malware attacks . The purpose of this slide which industries need to be alert while keeping confidential information safe from cyber attacks . Some industries are government, education , healthcare, manufacturing.Presenting our well structured Top Industries Effected By Malware Attack. The topics discussed in this slide are Top Industries Effected, Malware Attack. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
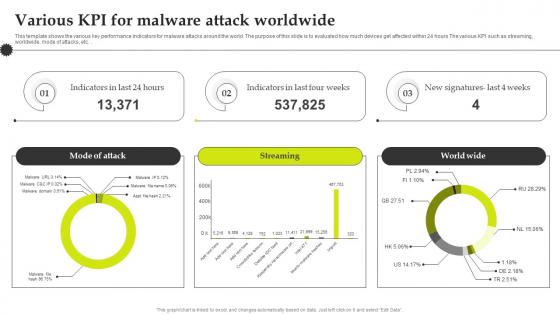
This template shows the various key performance indicators for malware attacks around the world. The purpose of this slide is to evaluated how much devices get affected within 24 hours The various KPI such as streaming, worldwide, mode of attacks, etc.Introducing our Various Kpi For Malware Attack Worldwide set of slides. The topics discussed in these slides are Various KPI For Malware, Attack Worldwide . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
Introducing our premium set of slides with Cyber Threat Icon Indicating Malware Attack. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Icon Indicating Malware Attack. So download instantly and tailor it with your information.
This slide represents the malware threat of cloud security and how it can affect data stored on the cloud, further leading to company loss. Introducing Cloud Security Threats Malware Attacks Cloud Data Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispense information on Frameworks, Targets, Technology, using this template. Grab it now to reap its full benefits.
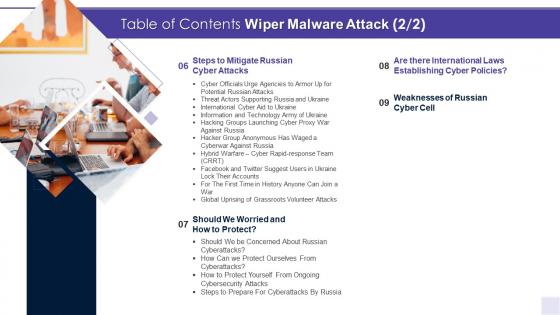
Introducing A36 Table Of Contents Wiper Malware Attack Ppt Styles Design Templates to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Protect, Cyber Attacks, Weaknesses, Cyber Policies, using this template. Grab it now to reap its full benefits.
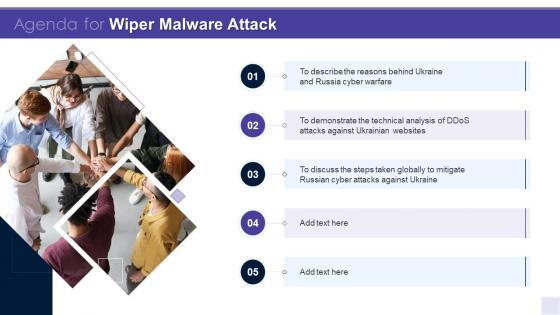
Increase audience engagement and knowledge by dispensing information using Agenda For Wiper Malware Attack Ppt Slides Vector. This template helps you present information on five stages. You can also present information on Cyber Warfare, Mitigate, Demonstrate, Technical using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
Presenting our well crafted Icons Slide For Wiper Malware Attack Ppt Styles Background set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
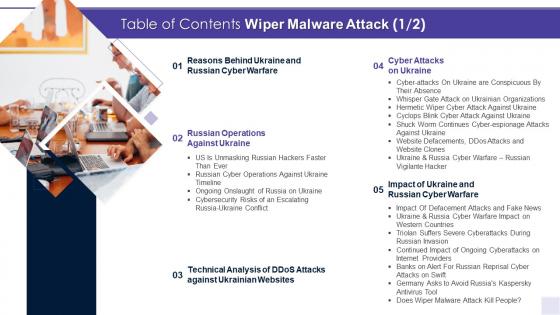
Introducing Table Of Contents Wiper Malware Attack Operations Ppt Styles Slide to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Operations, Technical, Websites, Impact, using this template. Grab it now to reap its full benefits.
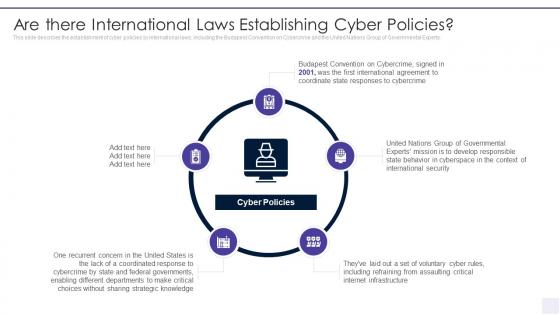
This slide describes the establishment of cyber policies by international laws, including the Budapest Convention on Cybercrime and the United Nations Group of Governmental Experts. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Are There International Laws Establishing Cyber Policies. This template helps you present information on five stages. You can also present information on Agreement, Coordinate, Responses, Convention, Security, Responsible using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

This slide represents that banks are on alert for Russian reprisal cyber attacks on Society for Worldwide Interbank Financial Telecommunication Swift. Introducing Wiper Malware Attack Banks On Alert For Russian Reprisal Cyber Attacks On Swift to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Transaction, Payment, Targeted, Payments, Institutions, using this template. Grab it now to reap its full benefits.
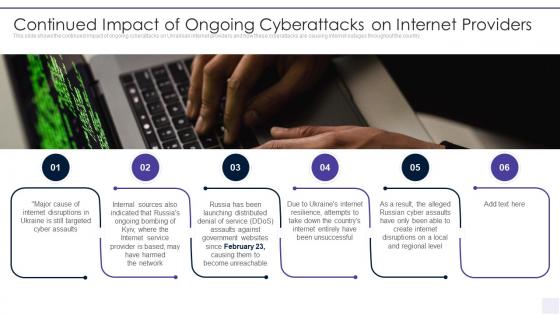
This slide shows the continued impact of ongoing cyberattacks on Ukrainian internet providers and how these cyberattacks are causing internet outages throughout the country. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Continued Impact Of Ongoing Cyberattacks. This template helps you present information on six stages. You can also present information on Internet Disruptions, Internal Sources, Resilience, Disruptions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

This slide represents the conspicuous Russian cyber attacks on Ukraine, including the attacks on government and banking websites, hacking of the countrys railway computer networks, etc. Introducing Wiper Malware Attack Cyber Attacks On Ukraine Are Conspicuous to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Public Relations, Discovered, Momentarily, Network, Conflict, using this template. Grab it now to reap its full benefits.

This slide represents that officials from the Department of Homeland Security have urged agencies to prepare for possible Russian cyberattacks, and CISA has amended its shields up guidelines. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Cyber Officials Urge Agencies To Armor. This template helps you present information on five stages. You can also present information on Cybersecurity, Corporations, Cyberattacks, Managers, Enterprises using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
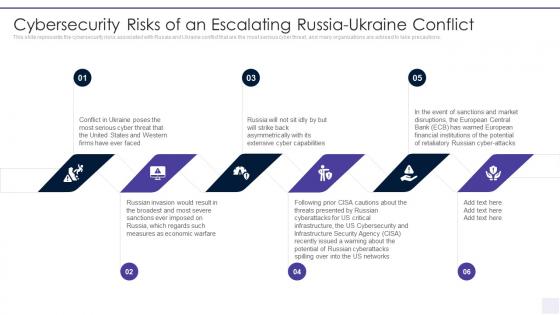
This slide represents the cybersecurity risks associated with Russia and Ukraine conflict that are the most serious cyber threat, and many organizations are advised to take precautions. Introducing Wiper Malware Attack Cybersecurity Risks Of An Escalating Russia to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Risks Of An Escalating Russia Ukraine Conflict, using this template. Grab it now to reap its full benefits.
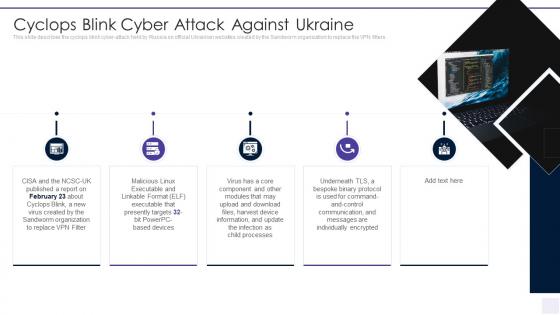
This slide describes the cyclops blink cyber attack held by Russia on official Ukrainian websites created by the Sandworm organization to replace the VPN filters. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Cyclops Blink Cyber Attack Against Ukraine. This template helps you present information on five stages. You can also present information on Cyclops Blink Cyber Attack Against Ukraine using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
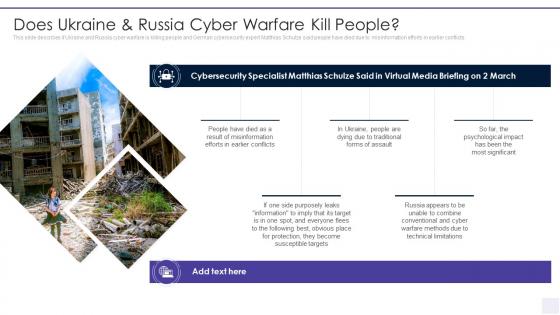
This slide describes if Ukraine and Russia cyber warfare is killing people and German cybersecurity expert Matthias Schulze said people have died due to misinformation efforts in earlier conflicts. Deliver an outstanding presentation on the topic using this Wiper Malware Attack Does Ukraine And Russia Cyber Warfare Kill People. Dispense information and present a thorough explanation of Cybersecurity, Traditional, Information, Misinformation, Susceptible using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.

This slide depicts Facebook and Twitters suggestion for Ukrainian citizens to close or lock their social media accounts as there are high chances of getting hacked in the hours of the war. Introducing Wiper Malware Attack Facebook And Twitter Suggest Users In Ukraine to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Disseminate, Disinformation, Intelligence, Prematurely, Techniques, using this template. Grab it now to reap its full benefits.

This slide represents the official announcement from Lotem Finkelstein, head of threat intelligence at Check Point Software, that anyone can join Ukraine and Russia cyber warfare. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack For The First Time In History Anyone Can Join A War. This template helps you present information on six stages. You can also present information on Volunteered, Digital, Participating, Organizations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

This slide depicts the official announcement to avoid Russias Kaspersky antivirus tool by German officials as Kaspersky has been accused of working for the Russian government. Introducing Wiper Malware Attack Germany Asks To Avoid Russias Kaspersky Antivirus Tool to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Information, Security, Enterprises, Prevention, Concerns, using this template. Grab it now to reap its full benefits.
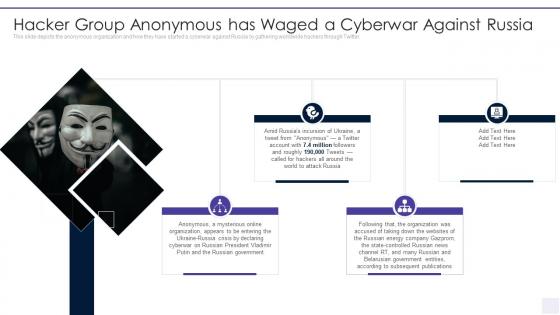
This slide depicts the anonymous organization and how they have started a cyberwar against Russia by gathering worldwide hackers through Twitter. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Hacker Group Anonymous Has Waged. This template helps you present information on four stages. You can also present information on Hacker Group Anonymous Has Waged A Cyberwar Against Russia using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
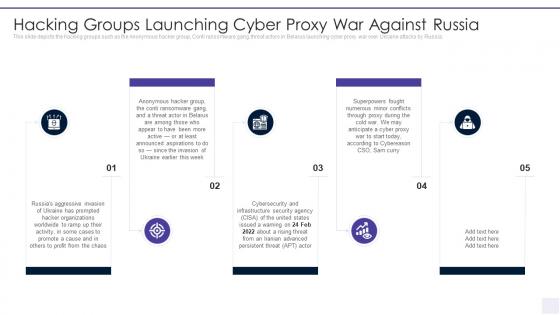
This slide depicts the hacking groups such as the Anonymous hacker group, Conti ransomware gang, threat actors in Belarus launching cyber proxy war over Ukraine attacks by Russia. Introducing Wiper Malware Attack Hacking Groups Launching Cyber Proxy to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Aggressive, Organizations, Promote, Invasion, Ransomware, using this template. Grab it now to reap its full benefits.

This slide depicts the hermetic wiper attack on Ukrainian corporations, detected by a threat intelligence agency on February 23rd, and it damaged the master boot record through Ease US Partition Master. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Hermetic Wiper Cyber Attack Against Ukraine. This template helps you present information on seven stages. You can also present information on Corporations, Malware, Agency, Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

This slide depicts cyberattacks protection methods to follow throughout the country, such as multi factor authentication, data backup, to keep a copy of all the backup information. Introducing Wiper Malware Attack How Can We Protect Ourselves From Cyberattacks to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Security, Administration, Authentication, using this template. Grab it now to reap its full benefits.
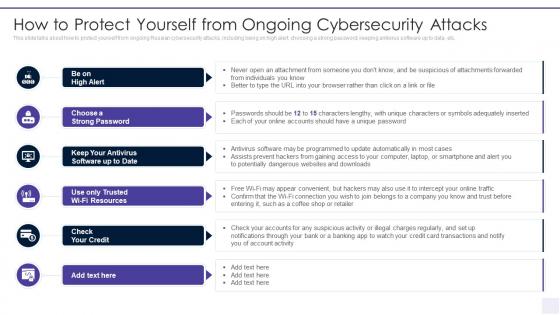
This slide talks about how to protect yourself from ongoing Russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack How To Protect Yourself From Ongoing. This template helps you present information on six stages. You can also present information on Convenient, Connection, Intercept, Notifications, Transactions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
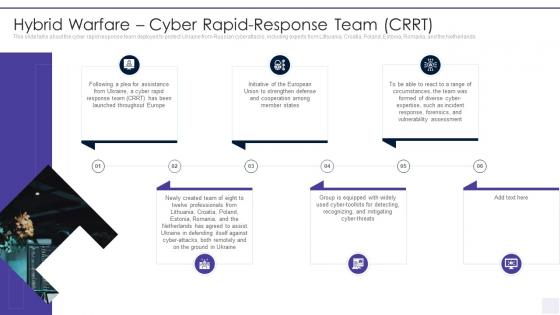
This slide talks about the cyber rapid response team deployed to protect Ukraine from Russian cyberattacks, including experts from Lithuania, Croatia, Poland, Estonia, Romania, and the Netherlands. Introducing Wiper Malware Attack Hybrid Warfare Cyber Rapid Response Team Crrt to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Strengthen, Cooperation, Vulnerability, Response, Assessment, using this template. Grab it now to reap its full benefits.

This slide shows the impact of defacement attacks and fake news on the public, and Meta has banned Russian media on its platforms, and Russia has restricted access to Facebook. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Impact Of Defacement Attacks And Fake News. This template helps you present information on eight stages. You can also present information on Information, Psychological, Deception, Fundamental, Trustworthy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

This slide represents the information and technology army of Ukraine, a Telegram group against Russia. In total, 308,000 users have joined this group to help Ukraine mitigate Russian cyber attacks. Introducing Wiper Malware Attack Information And Technology Army Of Ukraine to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information And Technology Army Of Ukraine, using this template. Grab it now to reap its full benefits.
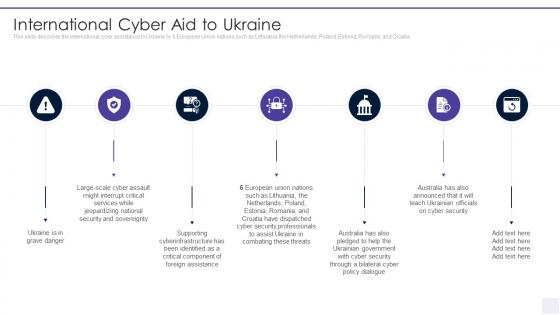
This slide describes the international cyber assistance to Ukraine by 6 European Union nations such as Lithuania, the Netherlands, Poland, Estonia, Romania, and Croatia. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack International Cyber Aid To Ukraine. This template helps you present information on seven stages. You can also present information on Interrupt, Assault, Jeopardizing, Sovereignty, Cyberinfrastructure using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

This slide represents the ongoing onslaught of Russia on Ukraine from December 2015 to Jan 2022. Russia has attacked Ukraine and other countries in many ways. Introducing Wiper Malware Attack Ongoing Onslaught Of Russia On Ukraine to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Infrastructure, Ransomware, Distributing, Electricity, Disruptions, Targeting, using this template. Grab it now to reap its full benefits.
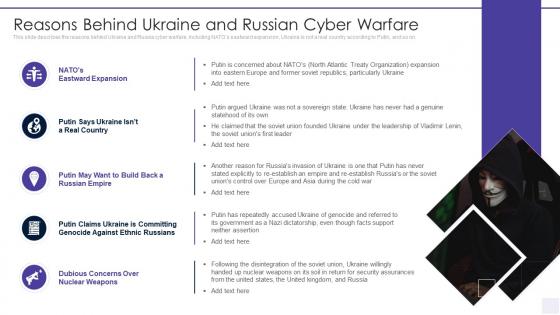
This slide describes the reasons behind Ukraine and Russia cyber warfare, including NATOs eastward expansion, Ukraine is not a real country according to Putin, and so on. Deliver an outstanding presentation on the topic using this Wiper Malware Attack Reasons Behind Ukraine And Russian Cyber Warfare. Dispense information and present a thorough explanation of Reasons Behind Ukraine And Russian Cyber Warfare using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
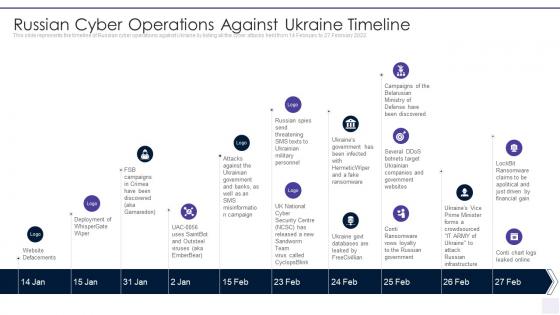
This slide represents the timeline of Russian cyber operations against Ukraine by listing all the cyber attacks held from 14 February to 27 February 2022. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Russian Cyber Operations Against Ukraine Timeline. This template helps you present information on ten stages. You can also present information on Russian Cyber Operations Against Ukraine Timeline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
This slide shows that US citizens should not be concerned about Russian cyberattacks as nothing has happened so far. However, the US Department of Homeland Security issued a warning to organizations to look for Russian cyberattacks. Introducing Wiper Malware Attack Should We Be Concerned About Russian Cyberattacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Security, Speculated, Cyberattacks, Unstoppable, using this template. Grab it now to reap its full benefits.

- Preferences

Types Of Malware PowerPoint PPT Presentations

Details of Malware and Their Types
May 16, 2019
90 likes | 121 Views
The Malware is used to refer to a huge selection of malicious applications. Here we have provided a list of common types of malware
Share Presentation
- malicious applications
- computer virus
- malicious worms
- computer security experts
- software provide free models

Presentation Transcript
Details of Malware • The Malware is coming from malicious applications and is used to refer to a software which is used to steal confidential information, cooperation company security and lead to damage to your computer or network. • The Malware is used to refer to a huge selection of malicious applications. Here we have provided a list of common types of malware that you must know about.
Virus • A computer virus is similar to a biological virus, except that it leaves your computer quite ill. It repeats and spreads to other computers by attaching itself onto apps, documents or files. • It subsequently implements a code when you open the infected file & also starts to infect your computer. • They may steal information, damage a system & host computer, cause financial harm and carry out much more deep & damaging results.
Ransomware • Ransomware is a type of malware which basically holds a PC system confined while demanding a ransom. • Most ransomware have been Trojans & spread through social engineering. in some cases, hackers reject to decrypt files even after you pay the ransom. • Ransomware can be avoided just like any other kind of malware application. All you have to know about how to remove ransomwarein case your system gets infected.
Trojan Horses • The trojan horse is a non-replicating application that looks legitimate. After obtaining the trust, it secretly performs malicious and malicious activities when implemented. • Hackers make use of trojan horses to steal a user's password data, terminate programs or data to the hard disk. It's challenging to detect.
Worms • Worms have existed even longer than viruses, all of the way back to mainframe days. • Email brought them into vogue in the late 1990s, and for nearly a period, computer security experts were surrounded by malicious worms which arrived as message attachments.
Spyware • Spyware, as the name implies, helps hackers spy on systems & their users. • This type of malware may be used to get key-logging and related tasks, thus helping hackers gain access to personal information including login IDs & intellectual property.
Adware • Adware or advertising-supported software is a kind of malware which automatically delivers advertisements. Typical examples of adware comprise pop-up ads on sites and ads that are displayed by applications. • Often times applications and software provide free models which come bundled with adware. Most adware is sponsored by advertisers & serves as a revenue creating tool.
Thank You Credits: ransomwares.net
- More by User
Analyzing Scorers: Their Details
Analyzing Scorers: Their Details. VAPG by: Carl Rainey DATCP, 608-224-5139. Overview. Basic problem areas Business viability Customer base/Increased returns Commitments of Support Management Team/Work Force Budget/Narrative. If you build it, they will come.
259 views • 11 slides
Hollywoodtoycoustmes and their types
Many people enjoy wearing super hero costumes at fancy dress and halloween events , looking for budget friendly
208 views • 5 slides
TYPES OF EPILEPSY AND THEIR MANAGEMENT
DR MUHAMMAD OMAR JAMIL MD. TYPES OF EPILEPSY AND THEIR MANAGEMENT. Definition of Seizures. Seizures are sudden, transitory, and uncontrolled episodes of brain dysfunction resulting from abnormal discharge of neuronal cells with associated motor, sensory or behavioral changes
1.08k views • 88 slides

Specific Types of Knowledge: Vocabulary and Details
Specific Types of Knowledge: Vocabulary and Details. Part I of 2 Page 291. Marzano considers strategies for four specific types of knowledge. Vocabulary terms and phrases Details Organizing Ideas Skills and Processes. The Research. 22 Point Percentile Gain in Student Achievement.
371 views • 23 slides
Types of Drugs and their Effects
Types of Drugs and their Effects. Amphetimines. Strong stimulant drugs that speed up the nervous system “Speed” Examples of amphetamines include methamphetamine, cocaine, and crack. Depressants. Do the opposite of Stimulants
954 views • 12 slides
Types of Rocks and Their Formation
Types of Rocks and Their Formation. Formation: Layers of sediment are deposited at the bottom of seas and lakes. Over millions of years, the layers get compressed by the layers above.
367 views • 13 slides
Common types of malware work as follows:
120 views • 2 slides
Types of details
Types of details. Facts - information that can be proven Fact: The first Super Bowl took place in 1967 in which the Green Bay Packers played the Kansas City Chiefs. Statistics - numbers about a specific topic
131 views • 4 slides
Types of tourists and their motivation
Types of tourists and their motivation (from Ryan, C. (1991) Recreational Tourism Routledge, London). Types of tourists and their motivation (from Ryan, C. (1991) Recreational Tourism Routledge, London)
252 views • 13 slides
Model Types and Their Basic Component Types
Model Types and Their Basic Component Types. Jim Carpenter 15 July 2001.
173 views • 2 slides
Types Of Fencing And Their Uses
Nothing can beat a good fencing mechanism or system when it is about protecting your property from burglars and thieves. Read more.
178 views • 2 slides

Types of adhesives and their importance
Some technicians use normal adhesive over the broken windshield, but it only creates a nuisance. This article will help you understand the two different types of adhesives and also the guide to choose the right adhesive for your windshield.
193 views • 14 slides

Nuts and their types
A nut is a type of a fastener with a threaded hole. Nuts are habitually used with a bolt, mating together to hold two objects together. A bolt or screw with an undercut is inserted through a hole and are secured with a nut, promoting sturdiness. Lock nuts prevent the loosening of bolts.
559 views • 9 slides
Aspects of Aluminum Wires and Their Details of Usages
This was not suitable for the branch type system of the electrical circuits. With the advent of new technology at this juncture, the aluminum wires were developed, which are known as the AA-800. This system was extremely compliant with the requirement of the branch based circuit system of the electricity. For more detail visit here@ http://www.ganpatiwires.com/aluminium-wire-rod.html
88 views • 6 slides
Malware and different types of malware
A computer virus is a malicious software that can copy itself onto multiple computers, in the process performing additional malicious tasks like corrupting data or destroying data. For more information.. https://hackercombat.com/malware-introduction-brief-history-different-kinds-malware/
164 views • 12 slides
Details About Types of Needles and Syringes
The most wide mentioned classifications of syringes are non Luer OK and Luer OK syringes.
56 views • 2 slides

Types of Anger and their impact
Types of Anger and their impact on various human being describe in this ppt
66 views • 6 slides
Types of ERP and their Applicability
The ERP software market is growing at a fast pace globally. The primary competition is between on-premise and cloud ERP. Read the blog to understand the difference between the two to help you to choose the suitable model for your business.
56 views • 5 slides
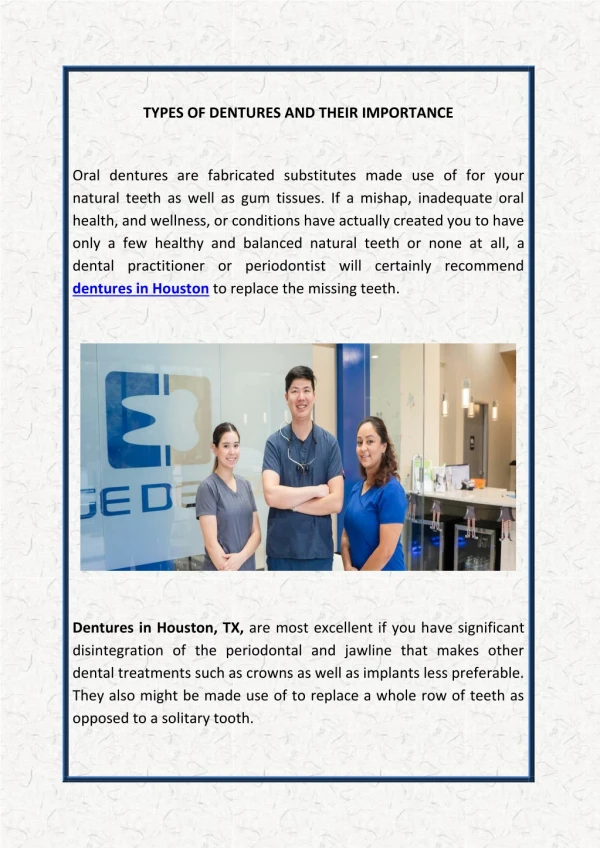
Types Of Dentures And Their Importance
Edge Dental are a Houston city dental care clinic who are available to treat patients with any dental issues they are experiencing. Contact us today by calling (281) 940-6960 to book an appointment with our experienced dentists in Houston, TX. Justin Lai DDS, a Family and Cosmetic Dentist in Houston, is Committed to Offering comprehensive care including dental checkups, cosmeticu00a0dentistry, dental implants & orthodontics, for the Whole Family in a Relaxed Environment.
49 views • 4 slides
Types of Computer Malware
Types of Computer Malware. The first macro virus was written for Microsoft Word and was discovered in August 1995. Today, there are thousands of macro viruses in existence—some examples are WM.concept, Melissa and Nimda.
278 views • 18 slides
Designation and types of flange connection details
RED EARTH Steels Pvt. Ltd. is a manufacturer of Alloy Steel WP22 Pipe Fittings in India, Supplier of ASTM A234 Gr WP22 Elbow, ASTM A234 WP22 class 3 Buttweld Fittings in Mumbai, Check Alloy Steel WP22 Elbow Price Online now.
23 views • 2 slides
Types of Windows and Their Features
The basic task of windows and doors is to let the air and light in. There are several kinds of windows and all of them have the same functions to follow. Their basic functionality is same, but they vary a lot on the basis of different factors. Some window types are easier to open while some ideal for broad views and some are great for airflow. - https://nuview.com.au/
120 views • 9 slides

IMAGES
VIDEO
COMMENTS
VIRUS Primitive types of malware. Possibly the most common type of malware, viruses attach their malicious code to clean code and wait for an unsuspecting user or an automated process to execute them. They are usually contained within an executable file. They are self- replicating programs that usually have a malicious intent. Instead it copies ...
12. Wiper Malware. A wiper is a type of malware with a single purpose: to erase user data and ensure it can't be recovered. Wipers are used to take down computer networks in public or private companies across various sectors. Threat actors also use wipers to cover up traces left after an intrusion, weakening their victim's ability to respond.
Malware, short for malicious software, refers to any intrusive software developed by cybercriminals (often called hackers) to steal data and damage or destroy computers and computer systems. Examples of common malware include viruses, worms, Trojan viruses, spyware, adware, and ransomware. Recent malware attacks have exfiltrated data in mass ...
The presentation introduced the concept of malware, types of malware, and methods for detecting malware. Benny provided examples of historical malware and illustrations of the difficulties that security vendors face in detecting threats.
malware (malicious software): Malware, or malicious software, is any program or file that is harmful to a computer user. Malware includes computer viruses, worms, Trojan horses and spyware. These malicious programs can perform a variety of functions, including stealing, encrypting or deleting sensitive data, altering or hijacking core ...
COURSE OBJECTIVES: • Have an intimate understanding of executable formats, Windows internals and API, and analysis techniques. • Extract investigative leads from host and network-based indicators associated with a malicious program. • Apply techniques and concepts to unpack, extract, decrypt, or bypass new antianalysis techniques in ...
The difference is that malware is an umbrella term for a range of online threats, including viruses, spyware, adware, ransomware, and other types of harmful software. A computer virus is simply one type of malware. Malware may be introduced to a network through phishing, malicious attachments, malicious downloads, social engineering, or flash ...
1 Introduction to MALWARE. Duygu KARAOĞLAN Murat ERGUN Can YÜCEL. 2 What is malware Can be loosely defined as "Malicious computer executable" A bit flexible definition Annoying software or program codes Running a code without user's consent "If you let somebody else execute code on your computer, then it is not your own computer ...
Malware Analysis: An Introduction. The paper will begin with an introduction describing the various types of malware. Types of malware described include Virus, Worms, Trojans, Adware, Spyware, Backdoors and Rootkits that can disastrously affect a Microsoft Windows operating system. The second section will discuss the basics of an...
Malware and different types of malware. An Image/Link below is provided (as is) to download presentation Download Policy: Content on the Website is provided to you AS IS for your information and personal use and may not be sold / licensed / shared on other websites without getting consent from its author. Download presentation by click this ...
Keep your employees up to date with the world of malware by editing and inserting these infographics into your presentations. You can provide data and statistics about different antivirus software and how to prevent hacking, phishing and other things. Our designs come in various forms: banners, pie charts, bar graphs...
In this presentation on what is malware? we will get to understand malware explained, what are malware and its types? We will also know specifically about viruses and trojans, their operation process, types of malicious programs, and how to prevent a malware attack. Through this, we can protect our system from getting infected with malware programs. The topics covered in this malware, virus ...
Malware is used by hackers for gaining access to sensitive information or data for financial gain. Viruses, worms, trojans are all different types of malware. Malware examples include viruses, worms, Trojan viruses, spyware, adware, and ransomware. Virus Viruses are the most common types of malware. A virus is not a standalone program and in ...
Spyware - Its purpose is to steal private information from a computer system for a third party. Spyware collects information and sends it to the hacker. Logic Bombs - A logic bomb is a malicious program that uses a trigger to activate the malicious code. The logic bomb remains non-functioning until that trigger event happens.
This easy-to-customize presentation on Malware Analysis will stun your audience with its captivating layouts. Available for PowerPoint and Google Slides! ... security professionals, incident responders, and IT administrators can make use of this superb set to showcase the types of malware analysis static, dynamic, manual, and automated. You can ...
Presentation Transcript. Types of Computer Malware. The first macro virus was written for Microsoft Word and was discovered in August 1995. Today, there are thousands of macro viruses in existence—some examples are WM.concept, Melissa and Nimda. A logic bomb employs a code that lies hidden until specific conditions are met.
180. Slide 1 of 67. Wiper Malware Attack Powerpoint Presentation Slides. This complete presentation has PPT slides on wide range of topics highlighting the core areas of your business needs. It has professionally designed templates with relevant visuals and subject driven content. This presentation deck has total of sixty two slides.
During download, if you can't get a presentation, the file might be deleted by the publisher. E N D . Presentation Transcript. 5 Types Of Malware Analysis The process of identifying and minimising possible dangers in a website, application, or server is known as malware analysis. It is an essential procedure that guarantees sensitive data ...
There are many types of malware namely bots, adware, worms, Trojan horses, spyware, virus, ransom ware and so on. Malware is an abbreviation for 'malicious software'. It is a software program or a script which is created with the intention of intruding and creating damage to computer systems.
Details of Malware and Their Types . Details of Malware • The Malware is coming from malicious applications and is used to refer to a software which is used to steal confidential information, cooperation company security and lead to damage to your computer or network. • The Malware is used to refer to a huge selection of malicious applications. Here we have provided a list of common types ...